5 Ways Security Testing Can Aid Incident Response
The importance for organizations to understand who their adversaries are and how they operate against their enterprise environments cannot be understated. An organization’s approach to cybersecurity testing and resilience improvements in the face of an increasingly volatile threat landscape must be underpinned around this perspective.
The core elements of a well-designed cybersecurity testing program should be to help the organization identify and remediate vulnerabilities, continuously challenge detection and response capability, refine threat intelligence gathering priorities, and enhance overall incident preparedness through continuous stress-testing of response plans. The Cost of a Data Breach 2022 report from IBM shows the average breach cost savings for organizations that regularly test incident response plans is $2.66 million (circa £2 million).
Although there is no one-size-fits-all solution, here are five key considerations that organizations can focus on while developing an overarching strategy to build and maintain a cybersecurity testing program.
1. Collaborate Across Teams
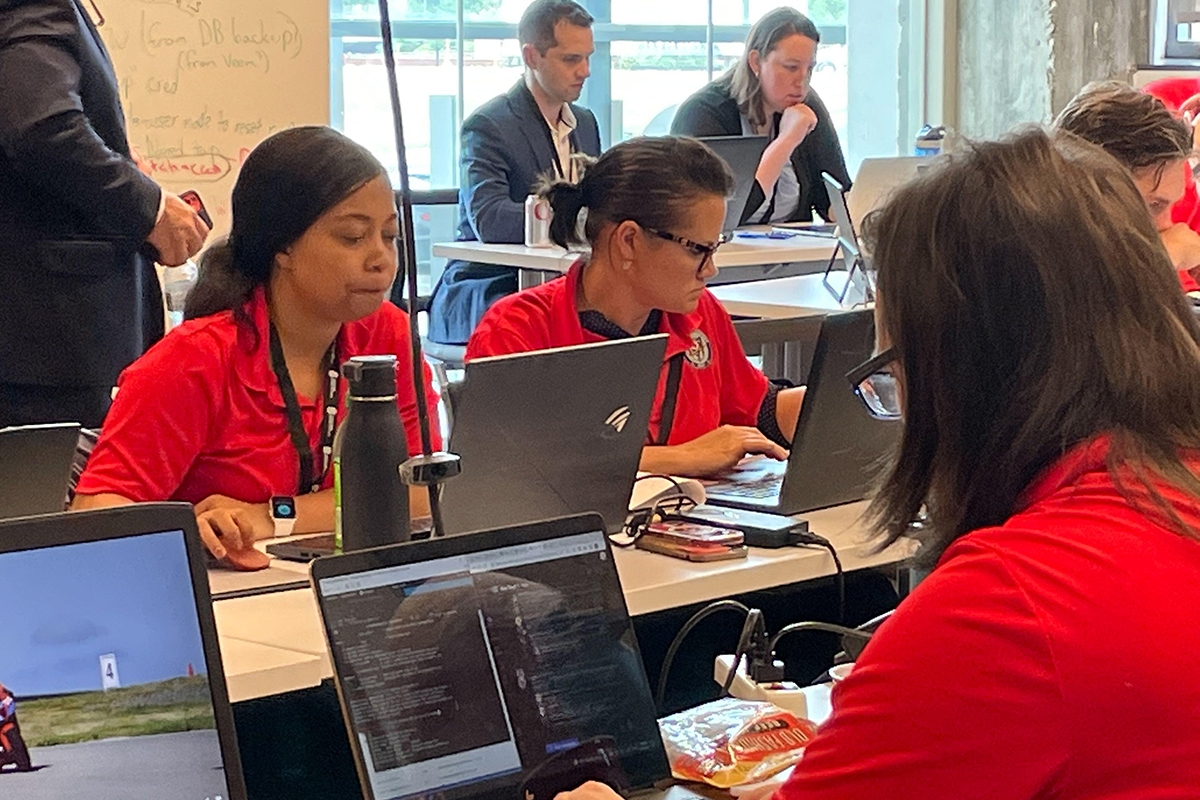
Collaboration is where the organization’s strength lies, so security teams should focus on building out internal relationships with different groups. Security teams should remember that the human component is critical and define a clear process to effectively allow representatives from the security operations center (SOC), risk / compliance, vulnerability management (VM), cyber threat intelligence (CTI), and security testing functions to drive collaboration.
Where possible, encourage these teams to have in-person discussions. This will create an opportunity for cross-team rapport at a personal level and develop a sense of camaraderie that will go a long way in achieving a common goal.
Creating a governance framework that defines clear responsibilities and promotes transparent communications between these teams to share findings quickly will allow for better decision-making, faster incident response, and a well-rounded appreciation of the organization’s cyber capabilities.
Collaboration allows for an enhanced appreciation of each other’s techniques and methods, as well as the exchange of knowledge and expertise to improve threat detection and mitigation strategies.
2. Follow an Intelligence-Led and Risk-Based Approach to Scope Definition
A process to continuously curate threat intelligence should enable organizations to build and maintain a comprehensive and up-to-date library of baseline attack scenarios. First, determine which threat actor groups are likely motivated to target the organization. Overlaying this with established baseline scenarios will help define a comprehensive list of tactics, techniques, and procedures (TTPs).
Organizations often have several assets in their environment, which makes identifying risk points and assessing where and how much money should be spent on vulnerability identification and remediation difficult. It may not be realistic from a timing perspective to assess the full list of identified TTPs against all the assets in scope.
A more risk-based approach is to carve out a plausible subset of TTP sequences and creatively mix-and-match infrastructure and software details, without being bound to an extensive checklist. This creates targeted sub-scenarios for the attack simulation team to initially focus on.
This approach will help CISOs more granularly measure the strength of practical mitigations that exist and identify high priority areas across critical business services, while optimally utilizing existing resources.
3. Perform Continuous Stress-Testing of Cyber Defense Controls
Leverage the scenarios and prioritized list of TTPs defined to constantly exercise the organization’s technical and business response. The scenarios subset should increase in complexity as the incident response program matures. Where the security team failed previously, these scenarios must be repeated so the organization can improve process in the event of a real attack.
It is important to select “low-and-slow” tactics that the SOC can detect and the VM team can remediate — but don’t make things too easy. Carefully selecting TTPs that are harder for the SOC to defend against encourages these teams to constantly sharpen their technique, as well as push the organization to update response strategies.
The choice between complexity, stealth, and speed will be driven by the organization’s risk profile and threat priorities that have contributed to shaping the specific scenario for testing.
4. Set Metrics for Shared Understanding and Improvement Tracking
Success criteria need to be defined and tracked to demonstrate overall risk reduction to organizational assets. Metrics such as reduced detection and/or response times, a decrease in successful attacks, and so on are useful to effectively articulate improvements to the board.
It is useful to compare results of previous and subsequent penetration tests, red team exercises, and/or targeted attack simulations, focusing on the number of high-risk vulnerabilities identified and exploited, as well as the overall success rate for the testers.
Being able to analyze changes in the threat landscape and demonstrate an increased ability to mitigate current and evolving threats will help CISOs demonstrate improved risk reduction.
5. Establish Feedback Channels to Drive Process Improvements
Break down test observations against executed TTPs along with actionable mitigations identified along the attack chain. Test results will also provide an improved understanding of which vulnerabilities are most likely to be exploited and can help refine risk prioritization in the VM process.
Sharing these results in real time to the CTI team allows them to monitor for potential threats that may exploit vulnerabilities, improves theoretical understanding of documented threats, and provides insight into previously unknown vulnerabilities, as well as helps prioritize areas for further research and analysis.
A centralized dashboard to aggregate test outputs in real time from the field, which can provide the relevant SOC team stakeholders with gaps identified in security monitoring tools and alerting systems, is extremely useful.
Providing a training range to practice and validate IR plans, and to identify areas where response times must be improved, is useful to improve overall incident preparedness.
The End Goal
The WEF Global Cybersecurity Outlook 2023 states that 43% of business leaders believe that their organization is likely to be hit by a major attack within the next two years. An all-encompassing change to cybersecurity testing, through increased collaboration and improved risk management processes, enhances resilience to cyberattacks.
Read More HERE
