Microsoft warns of current Nobelium phishing campaign impersonating USAID
Microsoft has warned that Nobelium is currently conducting a phishing campaign after the Russian-backed group managed to take control of the account used by USAID on the email marketing platform Constant Contact.
The phishing campaign has targeted around 3,000 accounts linked to government agencies, think tanks, consultants, and non-governmental organisations, Microsoft said. The US had received most of the malicious email, but it had reached 24 countries at a minimum.
“Nobelium launched this week’s attacks by gaining access to the Constant Contact account of USAID,” Microsoft corporate vice president of customer security and trust Tom Burt said.
“From there, the actor was able to distribute phishing emails that looked authentic but included a link that, when clicked, inserted a malicious file used to distribute a backdoor we call NativeZone. This backdoor could enable a wide range of activities from stealing data to infecting other computers on a network.”
Burt added that many of the emails were blocked, and there is no reason to think the attacks involve any vulnerability in Microsoft products.
The campaign was discovered in February, and Microsoft observed how Nobelium was changing its approach to getting its malicious code onto victim computers, a post from the Microsoft Threat Intelligence Center (MTIC) said.
In one instance, if a Nobelium-controlled server detected an Apple iOS device, it served up a WebKit universal cross site scripting vulnerability. Apple said on Wednesday it was aware of the vulnerability being actively exploited.
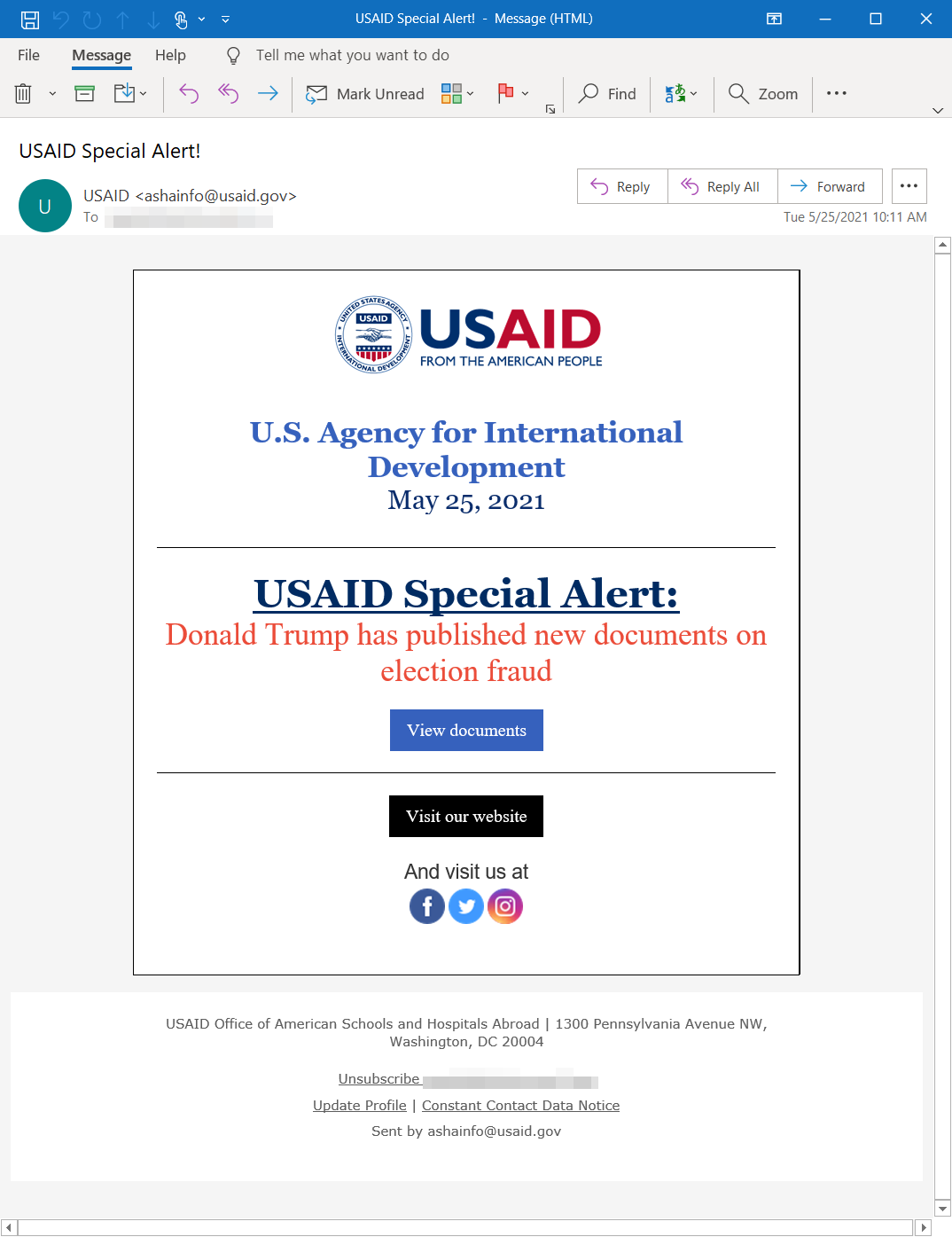
“In the May 25 campaign, there were several iterations. In one example the emails appear to originate from USAID, while having an authentic sender email address that matches the standard Constant Contact service,” MTIC said.
“This address (which varies for each recipient) ends in @in.constantcontact.com … and a Reply-To address of was observed.”
Once the link is clicked, a malicious ISO is delivered that contains a decoy document, a shortcut, and a malicious DLL with a Cobalt Strike Beacon loader that Microsoft has named NativeZone. If the shortcut is run, the DLL is executed and Nobelium is off to the races.
“The successful deployment of these payloads enables Nobelium to achieve persistent access to compromised machines,” MTIC said.
“Then, the successful execution of these malicious payloads could enable NOBELIUM to conduct action-on objectives, such as lateral movement, data exfiltration, and delivery of additional malware.”
MTIC added the Cobalt Strike Beacons use port 443 to call out to command and control infrastructure, and provided an indicators of compromise list in its post.
“It’s clear that part of Nobelium’s playbook is to gain access to trusted technology providers and infect their customers. By piggybacking on software updates and now mass email providers, Nobelium increases the chances of collateral damage in espionage operations and undermines trust in the technology ecosystem,” Burt said.
“This is yet another example of how cyberattacks have become the tool of choice for a growing number of nation-states to accomplish a wide variety of political objectives, with the focus of these attacks by Nobelium on human rights and humanitarian organisations.”
Burt called for rules related to how nations operating online, and for there to be consequences for violations.
“Microsoft will continue to work with willing governments and the private sector to advance the cause of digital peace,” he said.
Nobelium has been best known for the SolarWinds supply chain hack that saw a backdoor planted in thousands of organisations before cherrypicking nine US federal agencies and about 100 US companies to actually compromise and steal information from.
Microsoft has previously called out pieces of malware used by the group.
Mimecast said in March some of its source code and customer records was taken as part of the SolarWinds attack.
Related Coverage
READ MORE HERE
