Decade-Old Efail Attack Can Decrypt Previously Obtained Encyrpted Emails
Unfixed bugs in widely used email programs make it possible for attackers to obtain the plaintext of messages that are encrypted using the PGP and S/MIME standards, researchers said early Monday morning. The attacks assume that an attacker has possession of the encrypted emails and can trick either the original sender or one of the recipients into opening an invisible snippet of the intercepted message in a new email.
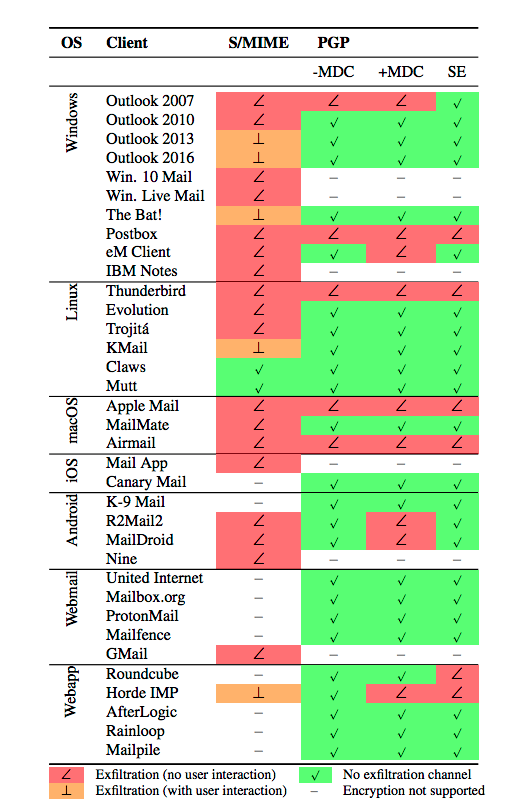
The flaws, some of which have existed for more than a decade, are part of a series of vulnerabilities dubbed Efail described by a team of European researchers. The vulnerabilities allow attackers to exfiltrate email plaintexts by embedding the previously obtained ciphertext into unviewable parts of an email and combining it with HTML coding. Earlier on Monday, the researchers and the Electronic Frontier Foundation issued an advisory recommending PGP and S/MIME users disable the encryption in their email clients but had planned to wait until Tuesday to provide technical details of the vulnerabilities. Within hours, the researchers published the paper, which is titled Efail: Breaking S/MIME and OpenPGP Email Encryption using Exfiltration Channels.
The most serious vulnerabilities have resided in Thunderbird, macOS Mail, and Outlook for more than 10 years and remain unfixed at the moment, the researchers said. Flaws in the way the programs handle emails with multiple body parts make it possible to embed invisible snippets of previously obtained encrypted text in new emails. By also including the Web address of an attacker-controlled server, the newly sent emails can cause the programs to send the corresponding plaintext to the server. The surreptitious exfiltration works against both the PGP and S/MIME standards.
“If you use PGP or S/MIME for sensitive information then this is a big deal,” Matt Green, a professor specializing in encryption at Johns Hopkins University, told Ars on Monday. “It means that those emails are potentially not secure. There is a real attack that can be exploited by people that allows them to decrypt a lot of encrypted email.”
So far the researchers have been unable to develop a working exploit that works when emails are viewed as text rather than in HTML. That means a less disruptive way to mitigate the vulnerability is to disable HTML in email clients. The researchers said they believe it may be possible to exfiltrate plaintext even when HTML is disabled using several different methods. One involves attaching malicious PDF or Microsoft Word documents that exfiltrate itself when opened. Another potential method might make small changes to the plaintext to call it to leak to a server.
The researchers said they made the more drastic recommendation to temporarily disable PGP in email apps out of an abundance of caution. Even when people follow such advice, it’s still possible to send and receive encrypted mail, as long as the encrypting and decrypting happens in in an application that’s separate from the email client. EFF has much more advice here.
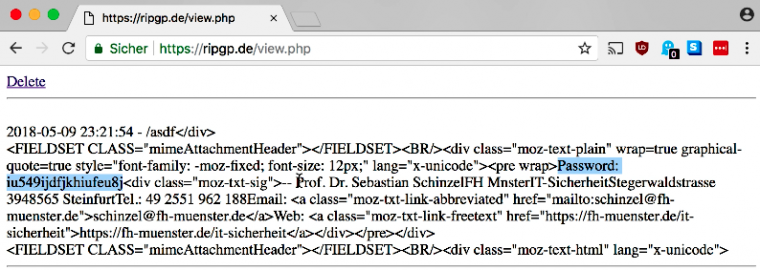
The following videos show Efail exploiting Thunderbird and Mac Mail. The videos are narrated by Sebastian Schinzel, a professor of computer security at Münster University of Applied Sciences and one of the authors of the paper.
The requirement that an attacker already have possession of an encrypted message is an important consideration. It means that the attacker would first have to break into an email server, take over an email account, intercept traffic as it crossed the Internet, or have access to a hard drive storing a previously sent email. The attacker would then have to get the sender or one of the receivers of the previously obtained message to open a new attacker-sent email. The new email would embed portions of the ciphertext in places that often aren’t displayed by Thunderbird, Mail, Outlook, and more than two-dozen other email programs. When done properly, the attack causes the corresponding plaintext of those snippets to be displayed on an attacker-controlled server.
While the requirement that attackers have access to previously sent emails is an extremely high bar, the entire purpose of both PGP and S/MIME is to protect users against this possibility. Ars will have much more coverage of the efail vulnerabilities, and the researchers have more information here.
In an email sent two hours after this post went live, Ryan Sipes, the community manager for the developer group that maintains Thunderbird, wrote: “A patch that addresses the last known exploit vector has been submitted, and is currently in review and being tested. We expect to see this land in an update to our users before the end of the week.” Apple representatives haven’t respond to a request for comment.
READ MORE HERE