Downloaders Currently the Most Prevalent Android Malware
Mobile malware — Android Trojans in particular — accounts for a small slice of overall malware activity, but it’s capable of doing more than just displaying adware. Some types of Android Trojans are capable of exfiltrating call data and GPS locations, for example.
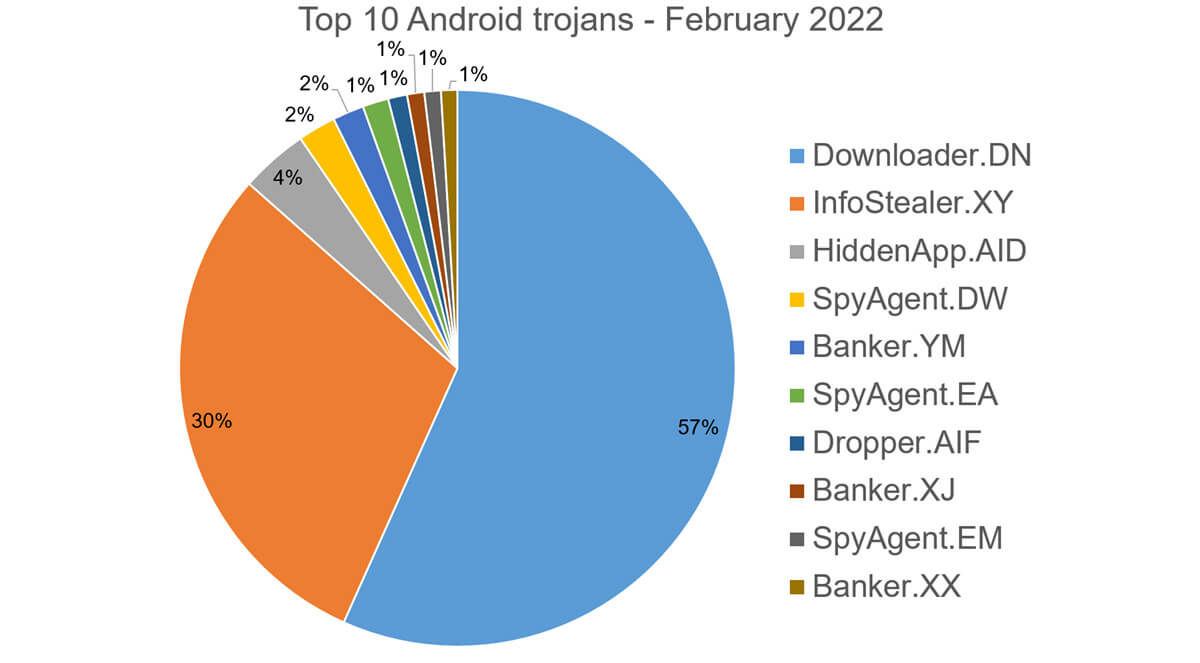
Downloaders and infostealers were the most prevalent types of Android Trojans in February, according to Bitdefender’s latest Threat Debrief, which looks at ransomware activity, mobile malware, and spoofed domains its telemetry detected during that month. Bitdefender’s Threat Debrief looks at detections, not infections. Bitdefender makes this distinction because detections mean the malicious code hit Bitdefender’s telemetry. It does not mean the malware successfully infected a device.
While Android apps bundled with malicious components are the most common type of Android malware, they are not the only types circulating. Bitdefender summarizes the top 10 Android Trojans detected in February in the Threat Debrief.
Top 3 Android Malware
The top 3 Trojans accounted for nearly 91% of the detections for the month.
- Downloader.DN refers to applications downloaded from the Google App Store and repackaged to include aggressive adware. Sometimes that adware is capable of downloading other types of malware.
- InfoStealer.XY are obfuscated applications masquerading as mobile antiviruses, capable of exfiltrating sensitive data, as well as downloading and installing other malware.
- HiddenApp.AID is a particularly aggressive adware that impersonates ad blockers. It asks for permission to display on top of other apps, which allows it to hide from the launcher.
Less Common Types of Android Malware
The remaining 7 Trojans made up less than 10% of detections.
- SpyAgent.DW exfiltrates sensitive data like SMS messages, call logs, contacts, or GPS location. SpyAgent.EA and SpyAgent.EM are similar in that they exfiltrate sensitive call data.
- Banker.YM grants device admin privileges and gains access to manage phone calls and text messages. It maintains a connection with the C&C server to receive commands and upload sensitive information. Banker.XJ has similar capabilities. Banker.XX impersonates Korean banking applications to record audio and video, collect sensitive information, and upload it to a C&C server.
- Dropper.AIF is a polymorphic app that drops and installs encrypted modules. Its icons are hidden from the launcher, making it difficult to detect.
Read More HERE
