Earth Koshchei Coopts Red Team Tools in Complex RDP Attacks

Summary
- Earth Koshchei’s rogue remote desktop protocol (RDP) campaign used an attack methodology involving an RDP relay, rogue RDP server, and a malicious RDP configuration file, leading to potential data leakage and malware installation.
- Earth Koshchei is known for constantly innovating and using a variety of methods. In this campaign, they leveraged red team tools for espionage and data exfiltration.
- The spear-phishing emails used in Earth Koshchei’s campaign were designed to deceive recipients into using a rogue RDP configuration file, causing their machines to connect to one of the group’s 193 RDP relays.
- Earth Koshchei’s campaign showed significant preparation, registering more than 200 domain names between August and October of this year.
- The group used anonymization layers like commercial VPN services, TOR, and residential proxies to mask their operations, enhance their stealthiness, and complicate attribution efforts.
Red teaming provides essential tools and testing methodologies for organizations to strengthen their security defenses. Cybercriminals and advanced persistent threat (APT) actors pay close attention to new methods and tools red teams develop, and they may repurpose them with a malicious intent.
In October 2024, an APT group that Trend Micro tracks as Earth Koshchei (also known as APT29 and Midnight Blizzard), likely used a rogue remote desktop protocol (RDP) attack methodology against numerous targets. This methodology was described earlier in 2022 by Black Hills Information Security in detail. The attack technique is called “rogue RDP”, which involves an RDP relay, a rogue RDP server, and a malicious RDP configuration file. A victim of this technique would give partial control of their machine to the attacker, potentially leading to data leakage and malware installation.
Earth Koshchei’s rogue RDP campaign reached its peak on October 22, when spear-phishing emails were sent to governments and armed forces, think tanks, academic researchers and Ukrainian targets. These emails were designed to deceive recipients into using a rogue RDP configuration file attached to the message. When opened, this RDP configuration file would instruct the target computer to try to connect to a foreign RDP server through one of the 193 RDP relays Earth Koshchei had set up.
Even though many of the targeted organizations are likely to have outgoing RDP connections blocked, it is still possible that in some cases RDP connections were not; for example, like in a home office environment or organizations that have less strict security in place. In the attack setup, it is also possible to use a non-standard port for the RDP relay, thus avoiding firewall rules. We believe that the spear-phishing email wave was preceded by earlier, very targeted and barely audible campaigns that ended abruptly with a final loud bang on October 22.
Microsoft and Amazon publicly attributed the rogue RDP campaign to Midnight Blizzard and APT29, which we track as Earth Koshchei. While we cannot make an independent attribution with high confidence to Earth Koshchei, we noticed they used some of their typical tactics, techniques and procedures (TTP) in the campaign and we could significantly expand on the indicators of compromise (IOCs) that had been made public so far by Microsoft and Cert-UA.
The threat group behind Earth Koshchei is allegedly sponsored by the Russian Foreign Intelligence Service (SVR), according to US and UK law enforcement. Earth Koshchei is characterized by its persistent targeting of diplomatic, military, energy, telecom, and IT companies in Western countries over many years, with the motivation believed to be primarily espionage. Earth Koshchei is known for adapting their TTPs and has deployed several techniques in the past like password spraying, brute forcing dormant accounts and watering hole attacks.
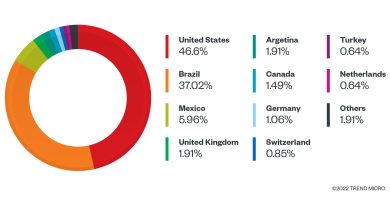
In Trend Micro’s global threat intelligence, the rogue RDP spear-phishing emails were found to have been sent to many targets, including the military, ministries of foreign affairs, targets in Ukraine and academic researchers. The scale of the RDP campaign was huge: The number of high-profile targets – about 200 – we saw in one day was about the same size as another APT group like Pawn Storm targets in weeks. This was not the first time Earth Koshchei was linked to a massive spear-phishing campaign: In May 2021, they also sent spear-phishing emails to thousands of individual accounts.
Preparations for the campaign had already started as early as August 7-8, when the adversary began to register domain names whose names suggest they would be used against targets that have a relationship with the Australian and Ukrainian governments. The last domain, registered on October 20, was apparently meant to target an organization with a link to the Netherlands’ Ministry of Foreign Affairs. In between, almost 200 domain names were registered, many of which suggest the target the adversaries had in mind.
This report aims to give a detailed explanation of what happened around Earth Koshchei’s RDP campaign, how the previously published red team methodology was used, to describe the scale of the campaign, and what anonymization layers were used. In particular, we discuss the infrastructure of the attack: We reveal 193 domains that were actively used against various organizations and 34 rogue RDP backend servers. In our assessment, these 193 domain names served as proxies to the 34 backends that look like the real rogue RDP servers of Earth Koshchei. We have seen evidence that some of the suspected rogue RDP backend servers, in combination with some of the RDP relays, were used for data exfiltration from October 18 to 21 for two military organizations and one cloud provider.
Rogue RDP configuration file: From red team tool to targeted attacks
We investigated one of the RDP configuration files that was sent to an academic researcher in Europe. The file specified a remote server to contact: eu-south-2-aws[.]zero-trust[.]solutions. Although the hostname suggests a legitimate Amazon Web Services (AWS) server, it is controlled by Earth Koshchei. The configuration redirects all local drives, printers, COM ports, smart cards, and clipboards, allowing remote access to the victim’s local machine. Obviously, this can be exploited for data exfiltration. After a successful connection is established, a remote application called AWS Secure Storage Connection Stability Test v24091285697854 is executed. At the time of our analysis, the remote servers were already down, so we could not check what action this remote application would execute.
Read More HERE