How to boost your incident response readiness
Cyberthreats are evolving with alarming sophistication, making it crucial for organizations to react swiftly to incidents and prepare for potential threats. Preparing your organization’s incident response readiness falls broadly into three categories: the process, the people, and the technologies. Often with cybersecurity, more focus is on the technology aspect. Although there is no question that technologies are essential, what sets successful incident response readiness and planning apart is a strong focus on the process and the people involved.
How the Microsoft Incident Response team helps customers remediate threats
This blog post, informed by insights from the Microsoft Incident Response team, will guide you through some key considerations of incident response readiness, structured through the people, process, and technology framework. Starting with the process, a key foundational piece, this blog post will provide guidance on actions such as:
- Developing a robust disaster recovery plan.
- Implementing a rigorous audit of admin accounts and services.
- Appointing an Incident Manager and outlining communication with vendors.
Read on to dive deeper into key technical concepts and actionable steps you can take to boost your incident response readiness and proactive threat engagements.
Microsoft Incident Response
Dedicated experts work with you before, during, and after a cybersecurity incident.

The process
Developing a disaster recovery plan
Developing a robust disaster recovery plan ensures business continuity and resilience against cyberthreats, natural disasters, or other disruptive events. This plan specifies the procedures and protocols for responding to security incidents, emphasizing rapid response, data recovery, and the restoration of critical services. Many companies prepare for fires, so why not incidents? Due to lack of continuity and organization of efforts, organizations without disaster recovery plans usually experience greater impact from unforeseen incidents.
When crafting a disaster recovery plan, conduct a comprehensive risk assessment to pinpoint potential threats, vulnerabilities, and single points of failure within your infrastructure. This step requires defining recovery objectives, prioritizing critical assets and services, and setting recovery time objectives and recovery point objectives based on business requirements and risk tolerance. Many organizations lack the personnel or capability to maintain an in-house incident response team and outsource with services like Microsoft Incident Response.
Disaster recovery plans often include recommendations like implementing a tiered approach to network recovery, managing on-site backups, performing off-site replication, and using cloud-based recovery services. These practices boost resilience and redundancy, minimizing downtime and data loss. Regularly testing and validating your plan with tabletop exercises, simulations, and drills is critical for identifying gaps, refining procedures, and ensuring readiness for real-world incidents.
When Microsoft Incident Response engages with customers that have disaster recovery plans in place, those plans have tremendously aided in ensuring business continuity. Pre-existing processes, warm backups, trained staff, and communication agreements with applicable vendors all empower the investigation and recovery efforts. Rather than developing a reactive disaster recovery plan in parallel with investigation efforts, an existing disaster recovery plan allows Microsoft Incident Response and the organization to focus on investigating threat actor actions. This also enables the organization’s staff to focus solely on bringing up their line of business apps. Engaging an incident response team alongside a comprehensive disaster recovery plan greatly expedites restoration time to keep your environment running.
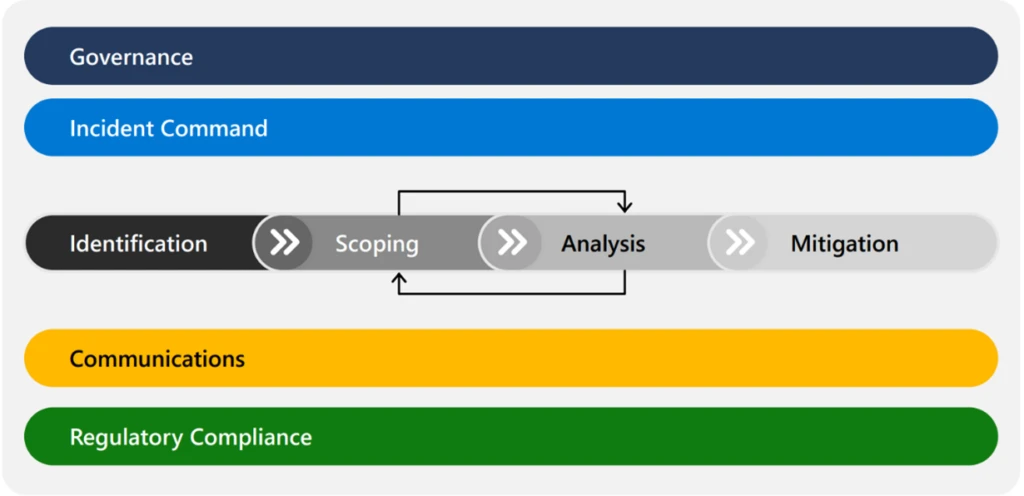
Figure 1. Workstreams that surround and support incident response throughout the lifecycle of an incident. See our team guide for context.
Validating effective deployment mechanisms
Ensuring the integrity and authenticity of software and system updates requires secure deployment mechanisms. Protect these systems—especially since threat actors often exploit them for tool deployment—by auditing their storage and configurations regularly. Adopting best practices like code signing, secure boot, and encrypted communications prevents unauthorized process tampering.
Correct setup requires varied deployment methods to be effective during incidents. Rapid tool deployment is important when working with an incident response team. Microsoft Configuration Manager, Microsoft Intune, Group Policy, and third-party tools are commonly used. Microsoft Incident Response deploys custom security tools alongside the Microsoft Defender suite to collect metadata efficiently across the environment, enabling a stronger response.
Enabling comprehensive auditing and logging
Auditing and logging are vital for a strong cybersecurity posture, offering insight into system activities and security events. Though enabling these features on all systems might increase overhead, the advantages in threat detection, incident response, and compliance outweigh the costs.
Adopting a risk-based approach to auditing and logging and focusing on critical assets and high-risk areas are essential. Configuring logs to capture relevant security events and optimizing retention policies ensure a balance between storage needs and forensic requirements.
Many Microsoft customers leverage Microsoft Sentinel, our cloud-native security information and event management (SIEM) solution for efficient large-volume data analysis. Microsoft Sentinel allows real-time log data aggregation, correlation, and analysis from various sources, aiding security teams in swift incident detection and response. Coupled with the Defender suite and Azure, Microsoft Sentinel offers invaluable trend data for incident response investigations.
The people
Appointing an incident manager for effective coordination
Appointing an Incident Manager is critical for leading and coordinating incident response efforts, from detection to recovery. This person serves as the main point of contact for stakeholders and response teams and ensures clear communication and effective collaboration. They examine, streamline, and log all environment change requests according to the disaster recovery plan.
An Incident Manager’s deep understanding of business processes and technical infrastructure aids in making informed decisions and prioritizing actions. Strong leadership and communication skills are essential for guiding teams and achieving consensus under pressure.
Without an Incident Manager, directionless and unclear communication allows threat actors to exploit chaos. A definitive leader streamlines work and facilitates clear communication, essential for efficient incident response. The absence of a coordinated effort can lead to fragmented work, prolonged network downtime, and severe access restoration delays for users or customers.
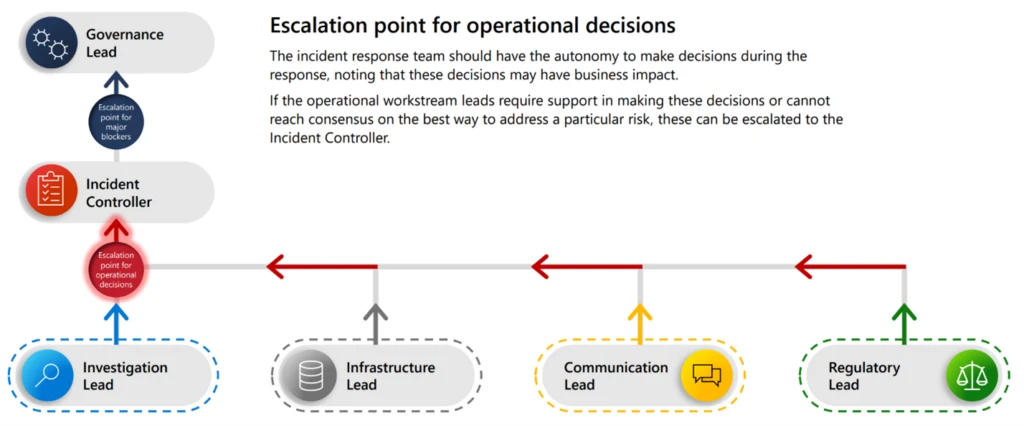
Figure 2. An example of the roles involved in incident response and the importance of an incident manager or controller. (See our team guide for more context.)
Maintaining open communication with security vendors
Open communication with security vendors is vital for enhancing cybersecurity. Strategic partnerships grant access to the latest technologies, threat intelligence, and best practices for threat management.
Security vendors assist in whitelisting tools, configuring policies, and optimizing security settings to meet standards and regulations. They also guide incident alert interpretation, remediation prioritization, and security measure implementation tailored to organizational needs.
Collaborating with vendors keeps organizations informed about emerging threats and attack techniques through threat intelligence feeds and security bulletins. This proactive intelligence sharing enables you to anticipate risks and mitigate them before security incidents escalate.
The technique
Enhancing security by hardening identity
Conduct a comprehensive Zero Trust audit on accounts and services with administrative privileges within your system to defend against potential security breaches effectively. This audit requires scrutinizing user and admin accounts, system configurations, and service permissions to spot anomalies or unauthorized access points. Leveraging robust identity and access management solutions is crucial to enforce the least-privilege principle. By giving users only the necessary permissions for their roles, organizations can significantly lower the attack surface and the risk of privilege escalation.
Use Enterprise Admins and Schema Admins, two built-in groups that can alter an Active Directory Forest, only for specific changes to the environment’s framework, then remove them. Also, you should audit AdminSDHolder, a common persistence method. Enforcing any privileges assigned to a user or group in the AdminSDHolder object remains effective regardless of changes in other Active Directory parts.
Microsoft Incident Response often recommends the enterprise access model or tiering to harden the identity plane for various environments. The tiering aims to protect identity (Tier 0) and all servers interacting with it, including Tier 0 management servers, all within the same plane. This model mandates administrators to have accounts in their specific plane, reducing the chances of lateral movement and privilege escalation.
Quick wins for safeguarding assets
When safeguarding accounts, methods like multifactor authentication introduce an additional security layer, making it harder for adversaries to compromise critical systems and data. Easy wins with multifactor authentication include enabling number matching and fraud alert, or mandating access through a Microsoft Entra-joined device.
Establishing an inactive (or stale) accounts policy is critical to reduce and eliminate potential entry points. Security vendors often create overprovisioned guest accounts that remain active until the contractor returns. Formulate a policy to disable and eventually delete accounts when not in use, marking a swift victory. A stale account policy, combined with a password policy and account lockout policy, helps secure the identity plane in an environment.
Proactively auditing services and machines
Auditing services and machines within the network is vital for identifying and mitigating security risks. Documenting the configurations and dependencies of all hardware and software assets, and assessing their vulnerability exposure, is important.
Automated asset management and vulnerability scanning tools streamline auditing and keep asset inventories current. Legacy software dependence, especially on unsupported systems, introduces vulnerabilities. Vulnerability scanning allows for proactive risk, patch, and configuration management, meeting security and compliance needs.
For best results, you should classify assets by criticality and sensitivity to prioritize security controls and resources. Distinguishing between protected legacy systems and risky end-of-life systems due to outdated or unsupported configurations is essential.
Driving incident response in your organization
Proactively preparing for incident response is essential given modern cybersecurity challenges. By strengthening defenses, maintaining a comprehensive disaster recovery plan, and leveraging expert resources like the Microsoft Incident Response team, you can confidently manage threats. Our expertise and quick response capabilities are invaluable in cyber risk mitigation.
Effective coordination and robust logging mechanisms reduce incident impacts and ensure operational resilience. Preparation is key in a world facing inevitable cyber threats. Learn more about Microsoft Incident Response proactive and reactive response services or find clarity in the maze of incident response in our helpful team guide.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us on LinkedIn (Microsoft Security) and X (@MSFTSecurity) for the latest news and updates on cybersecurity.
READ MORE HERE
