How to organize your security team: The evolution of cybersecurity roles and responsibilities
Digital transformation, cloud computing, and a sophisticated threat landscape are forcing everyone to rethink the functions of each role on their security teams, from Chief Information Security Officers (CISOs) to practitioners.
With billions of people around the globe working from home, changes to the daily practice of cybersecurity are accelerating. Organizations are shifting from defending a traditional network perimeter (keeping business assets in a safe place) to more effective zero trust strategies (protect users, data, and business assets where they are). This transformation brings technology changes and also opens up questions of what people’s roles and responsibilities will look like in this new world.
At the same time, continuous delivery models are requiring security teams to engage more closely during business planning and application development to effectively manage cyber risks (vs. the traditional ‘arms-length’ security approaches). This requires security professionals to better understand the business context and to collaborate more closely with stakeholders outside of security.
In this new world, traditional job descriptions and security tools won’t set your team up for success. Leaders must create role clarity in this transformation to help their teams navigate uncertainty. This will reduce distractions and stress, as well as help people focus on the important tasks that make the whole team shine.
While each organization and each person will have a unique journey, we have seen common patterns for successfully transforming roles and responsibilities. To help security leaders and practitioners plan for this transformation, Microsoft has defined common security functions, how they are evolving, and key relationships. In this blog, we’ll provide a summary of our recommendations to help you get started.
Security roles must evolve to confront today’s challenges
Security functions represent the human portion of a cybersecurity system. They are the tasks and duties that members of your team perform to help secure the organization. Depending on your company size and culture, individuals may be responsible for a single function or multiple functions; in some cases, multiple people might be assigned to a single function as a team.
High performing security teams understand their individual roles, but also see themselves as a larger team working together to defend against adversaries (see Figure 1). The following functions represent a fully populated enterprise security team, which may be aspirational for some organizations. Organizations often need to prioritize where to invest first based on their risk profile, available resources, and needs.
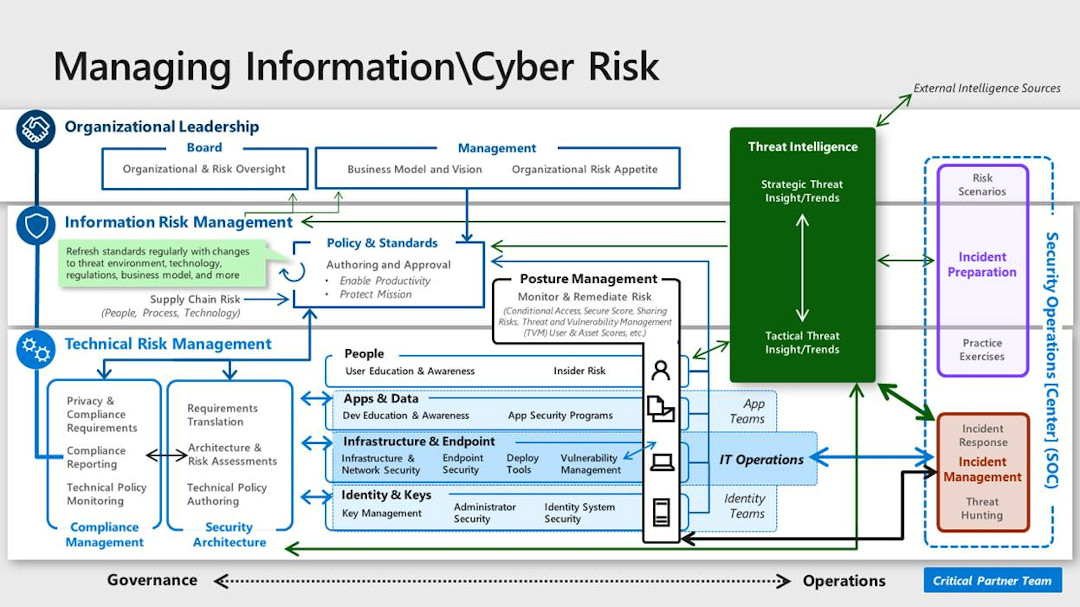
Figure 1: Each function works as part of a whole security team within the organization, which is part of a larger security community defending against the same adversaries.
Policy and standards
This team develops, approves, and publishes security policy and standards to guide security decisions within the organization and inspire change. This team must take into account cloud platforms, DevOps processes and tools, and relevant regulations, among other factors. Read more about security policy and standards function.
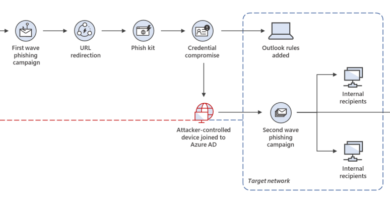
Security operations center (SOC)
A security operations center (SOC) detects, responds to, and remediates active attacks on enterprise assets. SOCs are currently undergoing significant change, including an elevation of the function to business risk management, changes in the types of metrics tracked, new technologies, and a greater emphasis on threat hunting. Read more about the SOC function.
Security architecture
Security architecture translates the organization’s business and assurance goals into a security vision, providing documentation and diagrams to guide technical security decisions. A modern architecture function needs to consider continuous delivery, identity-centric security solutions for cloud assets, cloud-based security solutions, and more. Read more about the security architecture function.
Security compliance management
The objective of cloud security compliance management is to ensure that the organization is compliant with regulatory requirements and internal policies. As you modernize this function, consider the role that cloud providers play in compliance status, how you link compliance to risk management, and cloud-based compliance tools. Read more about the security compliance management function.
People security
People security protects the organization from inadvertent human mistakes and malicious insider actions. The cloud and changing threat landscape require this function to consider how to effectively engage employees in security, organizational culture change, and identification of insider threats. Read more about the people security function.
Application security and DevSecOps
The objective of application security and DevSecOps is to integrate security assurances into development processes and custom line of business applications.
Cloud services and APIs have enabled a faster delivery cadence and influenced the creation of the DevOps team model, driving a number of changes. The biggest change we see is the integration of security into the development process, which requires culture and process adjustments as each specialty adopt the best of each other’s culture. This function must also adopt an agile mindset and stay up to date on new tools and technologies. Read more about the application security and DevSecOps function.
Data security
The main objective for a data security team is to provide security protections and monitoring for sensitive enterprise data in any format or location. New regulations and data loss prevention models are influencing the evolution of this function, and the sheer volume of data being stored on numerous devices and cloud services has also had a significant impact. Read more about the data security function.
Infrastructure and endpoint security
The infrastructure and endpoint security function is responsible for security protection to the data center infrastructure, network components, and user endpoint devices. Software-defined datacenters and other cloud technologies are helping solve longstanding data center security challenges, and cloud services are transforming the security of user endpoint devices. Read more about the infrastructure and endpoint security function.
Identity and keys
The main objective of a security team working on identity management, is to provide authentication and authorization of humans, services, devices, and applications. Key and certification management provides secure distribution and access to key material for cryptographic operations (which often support similar outcomes as identity management).
One of the big changes is that identity and key/certification management disciplines are coming closer together as they both provide assurances on the identity of entities and enable secure communications. This function also plays a significant role in modernizing security by establishing an identity-based perimeter that is a keystone of a zero-trust access control strategy. Read more about the identity and keys function.
Threat intelligence
Security threat intelligence provides context and actionable insights on active attacks and potential threats to empower organizational leaders and security teams to make better (data-driven) decisions. Threat intelligence usually grows from a technical scope into servicing the larger organization with strategic, tactical, and operational (technical) threat intelligence. Read more about the threat intelligence function.
Posture management
Posture management builds on existing functions like vulnerability management and focuses on continuously monitoring and improving the security posture of the organization. Posture management is typically one of the largest changes because it supports decisions in many other functions using information that only recently became available because of the heavy instrumentation of cloud technology. This function includes zero-trust based access controls, real-time risk scoring, threat and vulnerability management, and threat modeling, among others. Read more about the posture management function.
Incident preparation
The primary objective for the incident preparation function is to build process maturity and muscle memory for responding to major incidents throughout the organization, including security teams, executive leadership, and many others outside of security. These practice exercises have become powerful tools to ensure stakeholders are informed and familiar with their role in a major security incident. Read more about the incident preparation function.
Looking forward
In the beginning of the journey, clarity is critical to shine a light on the path forward and the journey ahead. As you walk the path, healthy doses of empathy and continuous learning are key to maintaining forward momentum. Organizations should invest in both formal training and supporting self-directed exploration to ensure people get the knowledge they need and have the confidence to take the risks required to transform.
In addition to the cloud security functions guidance, Microsoft has also invested in training and documentation to help with your journey—see the CISO Workshop, Microsoft Security Best Practices, recommendations for defining a security strategy, and security documentation site.
To learn more about Microsoft Security solutions visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
READ MORE HERE