Millions Still Haven’t Patched Terrapin SSH Protocol Vulnerability

Roughly 11 million Internet-exposed servers remain susceptible to a recently discovered vulnerability that allows attackers with a foothold inside affected networks. Once they’re in, attackers compromise the integrity of SSH sessions that form the lynchpin for admins to securely connect to computers inside the cloud and other sensitive environments.
Terrapin, as the vulnerability has been named, came to light two weeks ago in a research paper published by academic researchers. Tracked as CVE-2023-48795, the attack the researchers devised works when attackers have an adversary-in-the-middle attack (also abbreviated as AitM and known as man-in-the-middle or MitM), such as when they’re positioned on the same local network and can secretly intercept communications and assume the identity of both the recipient and the sender.
In those instances, Terrapin allows attackers to alter or corrupt information transmitted in the SSH data stream during the handshake—the earliest connection stage, when the two parties negotiate the encryption parameters they will use to establish a secure connection. As such, Terrapin represents the first practical cryptographic attack targeting the integrity of the SSH protocol itself. It works by targeting BPP (Binary Packet Protocol), which is designed to ensure AitMs can’t add or drop messages exchanged during the handshake. This prefix truncation attack works when implementations support either the “ChaCha20-Poly1305” or “CBC with Encrypt-then-MAC,” cipher modes, which, at the time the paper was published, was found in 77 percent of SSH servers.
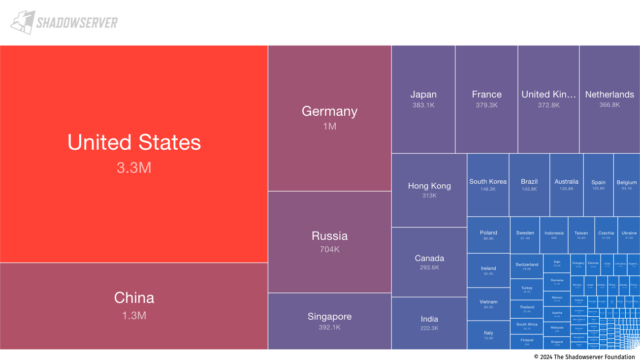
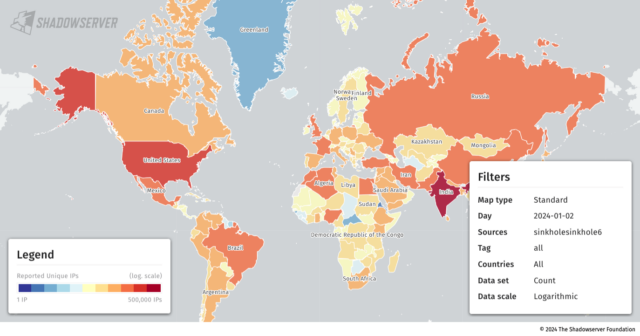
Internet-wide scans performed Tuesday, the last day such data was available at the time of reporting, revealed that more than 11 million IP addresses exposing an SSH server remained vulnerable to Terrapin. Nearly a third of those addresses, 3.3 million, resided in the US, followed by China, Russia, Germany, Russia and Singapore. All of the unpatched implementations tracked by Shadowserver supported the required cipher modes.
Only 53 of the vulnerable instances relied on implementations of AsyncSSH, the only app currently known to be seriously affected by Terrapin. Two vulnerabilities the researchers discovered in AsyncSSH allowed Terrapin to (1) downgrade security extensions that organizations to replace the extension information message sent by the server, letting the attacker control its content or (2) control the remote end of an SSH client session by either injecting or removing packets or emulating the shell established. AsyncSSH has patched those two vulnerabilities, tracked as CVE-2023-46445 and CVE-2023-46446, in addition to CVE-2023-48795, the Terrapin vulnerability affecting the SSH protocol. It appears the overwhelming majority of AsyncSSH users have installed the patches.
The requirement of an AitM position and the lack of currently known practical attacks made possible by Terrapin are important mitigating factors that some critics say have been lost in some news coverage. That said, at this stage, there are few good reasons not to have patched the protocol flaw by now, since patches became widely available about one to two weeks ago.
“The attack requires quite a bit of complexity in that MitM is necessary, so that will limit practical application to more targeted attacks in our view,” Piotr Kijewski, a Shadowserer researcher, wrote in an email to Ars. “So unlikely to have this mass-exploited. Still, the sheer mass of vulnerable instances suggests this vulnerability will be with us for years to come and that in itself makes it attractive in some specific cases.”
While it’s unlikely that Terrapin will ever be mass-exploited, the potential remains for it to be used in targeted attacks by more sophisticated attackers, such as those backed by nation-states. Despite earlier versions of AsyncSSH being the only known application vulnerable to practical Terrapin attacks, the researchers spent little time analyzing other implementations. Adversaries with more time, resources, and motivation could identify other vulnerable implementations.
Kijewski listed the top 50 banners displayed by vulnerable IP addresses as:
- serverid_software count
- openssh_7.4 2878009
- openssh_7.6p1 956296
- openssh_8.2p1 802582
- openssh_8.0 758138
- openssh_7.9p1 718727
- openssh_8.4p1 594147
- openssh_8.9p1 460595
- openssh_7.2p2 391769
- openssh_7.4p1 320805
- openssh_8.5 316462
- openssh_9.3 298626
- openssh_8.7 219381
- openssh_6.7p1 156758
- openssh_9.2p1 141010
- openssh_6.6.1p1 136489
- openssh_9.0 112179
- openssh_6.6.1 105423
- dropbear_2020.80 93154
- openssh_8.8 88284
- openssh_7.5 76034
- aws_sftp_1.1 75157
- openssh_9.0p1 70305
- openssh_8.2 59887
- openssh_7.9 59301
- dropbear 51374
- openssh 35408
- openssh_7.2 34494
- openssh_7.8 33955
- dropbear_2020.81 28189
- openssh_9.5 27525
- openssh_9.1 26748
- openssh_8.1 23188
- lancom 22267
- openssh_6.4 18483
- openssh_8.4 18158
- openssh_8.9 17310
- openssh_7.6 17235
- openssh_for_windows_8.1 17150
- openssh_for_windows_7.7 15603
- openssh_8.6 14018
- openssh_6.9 13601
- openssh_9.4 12802
- dropbear_2022.82 12605
- dropbear_2022.83 12036
- openssh_7.7 11645
- openssh_for_windows_8.0 11089
- openssh_7.3 10083
- mod_sftp 9937
- openssh_8.3p1 9163
- cisco-1.25 8301
Patching Terrapin isn’t straightforward, because of the sheer number of implementations affected and the necessity that apps running on both the admin client and the server be patched. The researchers listed the following implementations as vulnerable and included links to patches when available. Asterisks indicate application developers contacted prior to the release of the research paper:
| Implementation | Affected Versions | Patched Version(s) |
|---|---|---|
| AsyncSSH* | 2.14.1 and earlier | 2.14.2 |
| Bitvise SSH* | 9.31 and earlier | 9.33 |
| ConnectBot* | 1.9.9 and earlier | 1.9.10 |
| CrushFTP | 10.5.6 and earlier | 10.6.0 |
| CycloneSSH* | 2.3.2 and earlier | 2.3.4 |
| Dropbear* | 2022.83 and earlier | To be released |
| Erlang/OTP SSH* | OTP 26.2 and earlier OTP 25.3.2.7 and earlier OTP 24.3.4.14 and earlier |
OTP 26.2.1 OTP 25.3.2.8 OTP 24.3.4.15 |
| FileZilla Client | 3.66.1 and earlier | 3.66.4 |
| Golang x/crypto/ssh* | 0.16.0 and earlier | 0.17.0 |
| JSch (Fork)* | 0.2.14 and earlier | 0.2.15 |
| libssh* | 0.10.5 and earlier 0.9.7 and earlier |
0.10.6 0.9.8 |
| libssh2* | 1.11.0 and earlier | To be released |
| Maverick Legacy* | 1.7.55 and earlier | 1.7.56 |
| Maverick Synergy* | 3.0.21 and earlier (Hotfix) 3.0.10 and earlier (OSS) |
3.0.22 3.1.0-SNAPSHOT |
| MobaXterm | 23.5 and earlier | 23.6 |
| Nova | 11.7 and earlier | 11.8 |
| OpenSSH* | 9.5 / 9.5p1 and earlier | 9.6 / 9.6p1 |
| Paramiko* | 3.3.1 and earlier | 3.4.0 |
| phpseclib | 3.0.34 and earlier 2.0.45 and earlier 1.0.21 and earlier |
3.0.35 2.0.46 1.0.22 |
| PKIX-SSH* | 14.3 and earlier | 14.4 |
| ProFTPD* | 1.3.8a and earlier | 1.3.8b |
| PuTTY* | 0.79 and earlier | 0.80 |
| Russh* | 0.40.1 and earlier | 0.40.2 |
| SecureCRT* | 9.4.2 and earlier | 9.4.3 |
| SFTP Gateway | 3.4.5 and earlier | 3.4.6 |
| SFTPGo | 2.5.5 and earlier 2.4.5 and earlier |
2.5.6 2.4.6 |
| ssh2* | 1.14.0 and earlier | 1.15.0 |
| sshj* | 0.37.0 and earlier | 0.38.0 |
| Tera Term* | 5.0 and earlier 4.107 and earlier |
5.1 4.108 |
| Thrussh* | 0.34.0 and earlier | 0.35.1 |
| TinySSH | 20230101 and earlier | 20240101 |
| Transmit | 5.10.3 and earlier | 5.10.4 |
| Win32-OpenSSH* | 9.4.0.0p1-Beta | 9.5.0.0p1-Beta |
| WinSCP | 6.1.2 and earlier | 6.2.2 beta |
| XShell 7* | Build 0142 and earlier | Build 0144 |
As explained earlier, there’s little reason for mass alarm. Terrapin is no Citrix Bleed , CVE-2022-47966, MoveIT, CVE-2021-22986, or CVE-2023-49103, or CVE-2021-22986, which were some of the most exploited vulnerabilities of 2023 that led to the compromise of millions of servers. So far, there are no known reports of Terrapin patches causing side effects. Admins would do well to patch sooner rather than later. READ MORE HERE