Private 5G Security Risks in Manufacturing Part 3


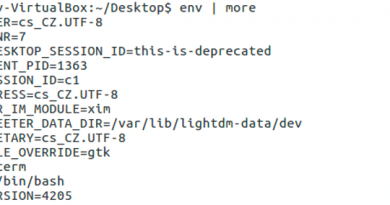
① CN hosting server
As Private 5G grows more and more mainstream going forward, we can expect organizations to use general-purpose servers to host their core networks with the aim to cut costs. We also used a regular x86 server to host the core network in our field test. As the trend toward open infrastructure continues, it is imperative to be vigilant of potential vulnerabilities being exploited in the core network hosting server. This is a crucially important area with respect to building the core network environment in a Private 5G configuration, considering that we are seeing an increase in both users and vulnerabilities in Linux OS.
② VM/Container
It is also imperative to consider the vulnerabilities in containers and other virtualized environments. At Trend Micro, we are aware of a type of attack called “container escape” in which the attacker can go through the container to infiltrate the host server. Container technology will play a big role in 5G core networks, and container images are largely made up of open-source packages such as SQL database engines and programming languages. As such, these packages require the same kind of precautions for code that was downloaded from an external source: Looking up who made the libraries, and reviewing the code to make sure it is not malicious. Considering that it is crucial to work closely with the system integrator when building a Private 5G configuration, the user organization (and asset owner) must proactively request the system vendor and integrator to implement security measures in the container environment.
③ Network infrastructure
Another avenue for infiltration is the network infrastructure, including routers and firewalls. Private 5G solutions use switches, routers, and other networking equipment in the core network. It is crucial to manage and mitigate vulnerabilities in this equipment just like for any regular IT system.
④ Base station
Base station security research still has a way to go at the moment, but we found some vulnerabilities with our tests. We escalated these vulnerabilities with the vendor, who said that this issue could only be found in the model sold for testing and not in the regular product. However, verification environments often include important documents and intellectual property, so it is crucial to secure the same level of security for equipment in the verification environment as in the production environment. In any case, we strongly recommend that the owner of the base station carries out penetration tests on site, and to check that the base is sufficiently protected and that there are no similar vulnerabilities in the production environment.
These are the four potential penetration routes that we identified in our research. These vulnerabilities in Private 5G configurations may not necessarily be exposed on the Internet for cyber attackers to access, though it is crucial to remember that vulnerabilities and attack methods can be shared widely as infrastructure becomes more open.
Three signal interception points
Once an attacker has got into the core network through one of the routes described above, they will go to the next phase: Intercepting and tampering with data. In our test, we identified three interception points within the user plane that processes user data (Fig. 2).
Read More HERE