Pro-Russian Hackers Target Elected US Officials Supporting Ukraine

Threat actors aligned with Russia and Belarus are targeting elected US officials supporting Ukraine, using attacks that attempt to compromise their email accounts, researchers from security firm Proofpoint said.
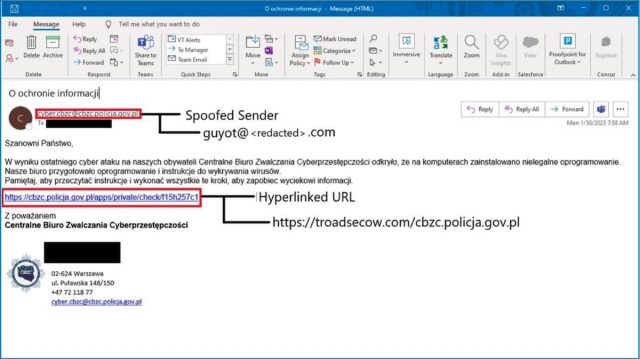
The campaign, which also targets officials of European nations, uses malicious JavaScript that’s customized for individual webmail portals belonging to various NATO-aligned organizations, a report Proofpoint published Thursday said. The threat actor—which Proofpoint has tracked since 2021 under the name TA473—employs sustained reconnaissance and painstaking research to ensure the scripts steal targets’ usernames, passwords, and other sensitive login credentials as intended on each publicly exposed webmail portal being targeted.
Tenacious targeting
“This actor has been tenacious in its targeting of American and European officials as well as military and diplomatic personnel in Europe,” Proofpoint threat researcher Michael Raggi wrote in an email. “Since late 2022, TA473 has invested an ample amount of time studying the webmail portals of European government entities and scanning publicly facing infrastructure for vulnerabilities all in an effort to ultimately gain access to emails of those closely involved in government affairs and the Russia-Ukraine war.”
Raggi declined to identify the targets except to say they included elected US officials and staffers at the federal government level as well as European entities. “In several instances among both US and European targeted entities, the individuals targeted by these phishing campaigns are vocal supporters of Ukraine in the Russia/Ukraine War and/or involved in initiatives pertaining to the support of Ukraine on an international stage,” he added.
Most of the recent attacks observed by Proofpoint exploited a vulnerability in outdated versions of Zimbra Collaboration, a software package used to host webmail portals. Tracked as CVE-2022-27926 and patched last March, the vulnerability is a cross-site scripting flaw that makes it possible for unauthenticated attackers to execute malicious Web scripts on servers by sending specially crafted requests. The attacks work only against Zimbra servers that have yet to install the patch.
The campaign begins with the use of scanning tools such as Acunetix to identify unpatched portals belonging to groups of interest. TA473 members then deliver phishing emails purporting to contain information of interest to the recipients.
READ MORE HERE


