Microsoft finds new NETGEAR firmware vulnerabilities that could lead to identity theft and full system compromise
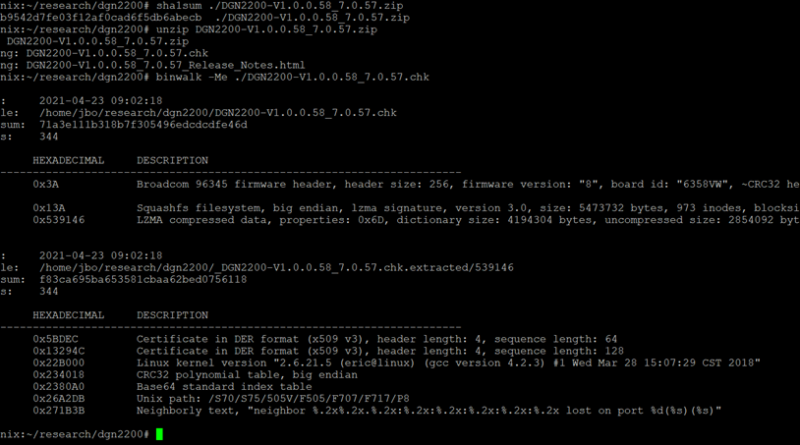
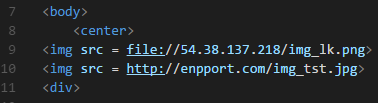
We discovered vulnerabilities in NETGEAR DGN-2200v1 series routers that can compromise a network’s security—opening the gates for attackers to roam untethered through an entire organization. We shared our findings with NETGEAR through coordinated vulnerability disclosure via Microsoft Security Vulnerability Research (MSVR), and worked closely with NETGEAR security and engineering teams to provide advice on mitigating these issues.
The post Microsoft finds new NETGEAR firmware vulnerabilities that could lead to identity theft and full system compromise appeared first on Microsoft Security Blog. READ MORE HERE…