Zero trust planning: Key factors for IT pros to consider
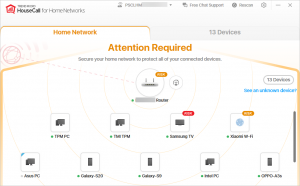
Moving away from VPNs as a means to protect corporate networks at the perimeter and moving toward zero-trust network access requires careful enterprise planning and may require implementing technologies that are new to individual organizations.ZTNA employs identity-based authentication to establish trust with entities trying to access the network and grants each authorized entity access only to the data and applications they require to accomplish their tasks. It also provides new tools for IT to control access to sensitive data by those entities that are deemed trusted.To read this article in full, please click here READ MORE HERE…