8220 Gang Evolves With New Strategies
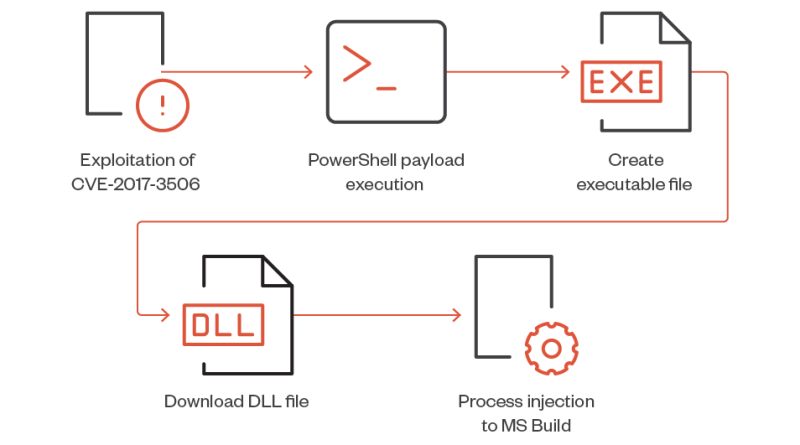
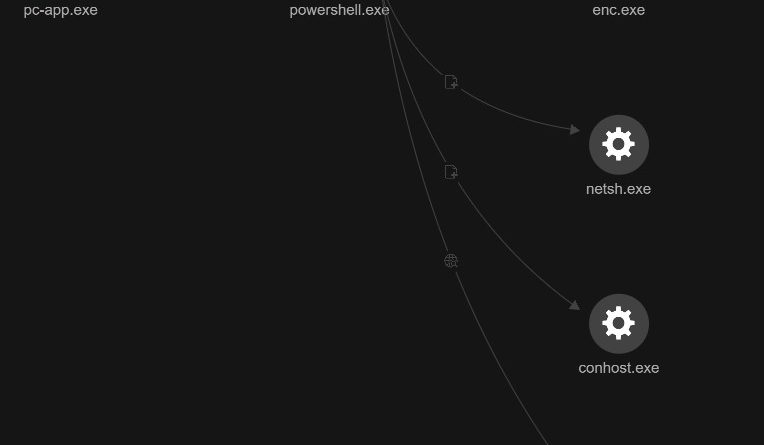
We observed the threat actor group known as “8220 Gang” employing new strategies for their respective campaigns, including exploits for the Linux utility “lwp-download” and CVE-2017-3506, an Oracle WebLogic vulnerability. Read More HERE…