These Are The Top Five Cloud Security Risks, Qualys Says
Cloud security specialist Qualys has provided its view of the top five cloud security risks, drawing insights and data from its own platform and third parties.
The five key risk areas are misconfigurations, external-facing vulnerabilities, weaponized vulnerabilities, malware inside a cloud environment, and remediation lag (that is, delays in patching).
The 2023 Qualys Cloud Security Insights report (PDF) provides more details on these risk areas. It will surprise no-one that misconfiguration is the first. As long ago as January 2020, the NSA warned that misconfiguration is a primary risk area for cloud assets – and little seems to have changed. Both Qualys and the NSA cite misunderstanding or avoidance of the concept of shared responsibility between cloud service providers (CSP) and cloud consumers is a primary cause of misconfiguration.
“Under the shared responsibility model,” explains Utpal Bhatt, CMO at Tigera, “CSPs are responsible for monitoring and responding to threats to the cloud and infrastructure, including servers and connections. They are also expected to provide customers with the capabilities needed to secure their workloads and data. The organization using the cloud is responsible for the protection of workloads running in the cloud. Workload protection includes secure workload posture, runtime protection, threat detection, incident response and risk mitigation.”
While CSPs provide security settings, the speed and simplicity of deploying data to the cloud often lead to these controls being ignored, while compensating consumer controls are inadequate. Misunderstanding or misusing the delineation of shared responsibility leaves cracks in the defense; and Qualys notes “these security ‘cracks’ can quickly open a cloud environment and expose sensitive data and resources to attackers.”
Qualys finds that misconfiguration (measured against the CIS benchmarks) is present in 60% of Google Cloud Platform (GCP) usage, 57% of Azure, and 34% of Amazon Web Services (AWS).
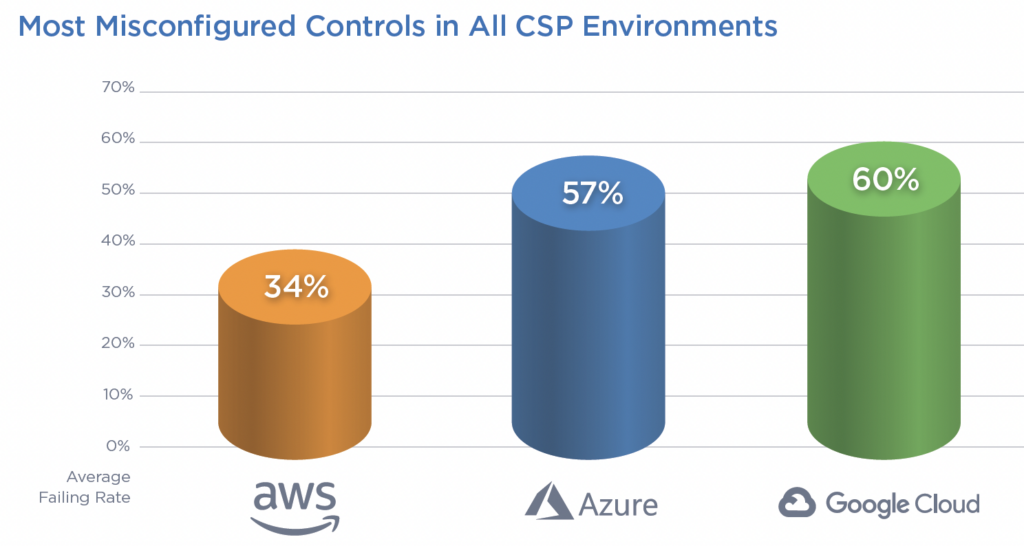
Travis Smith, VP of the Qualys threat research unit, suggests, “The reason AWS configurations are more secure than their counterparts at Azure and GCP can likely be attributed to the larger market share… there is more material on securing AWS compared to other CSPs in the market.”
The report urges greater use of the Center for Internet Security (CIS) benchmarks to harden cloud environments. “No organization will deploy 100% coverage,” adds Smith, “but the [CIS benchmarks mapped to the MITRE ATT&CK tactics and techniques] should be strongly considered as a baseline if organizations want to reduce the risk of experiencing a security incident in their cloud deployments.”
The second big risk comes from external facing assets that contain a known vulnerability. Cloud assets with a public IP can be scanned by attackers looking for vulnerabilities. Log4Shell, an external facing vulnerability, is used as an example. “Today, patches exist for Log4Shell and its known secondary vulnerabilities,” says Qualys. “But Log4Shell is still woefully under remediated with 68.44% of detections being unpatched on external-facing cloud assets.”
Log4Shell also illustrates the third risk: weaponized vulnerabilities. “The existence of weaponized vulnerabilities is like handing anyone a key to your cloud,” says the report. Log4Shell allows attackers to execute arbitrary Java code or leak sensitive information by manipulating specific string substitution expressions when logging a string. It is easy to exploit and ubiquitous across clouds.
“Log4Shell was first detected in December 2021 and continues to plague enterprises globally. We have detected one million Log4Shell vulnerabilities, with a mere 30% successfully fixed. Due to complexity, remediating Log4Shell vulnerabilities takes, on average, 136.36 days (about four and a half months).”
The fourth risk is the presence of malware already in your cloud. While this doesn’t automatically imply ‘game over’, it will be soon if nothing is done. “The two greatest threats to cloud assets are cryptomining and malware; both are designed to provide a foothold in your environment or facilitate lateral movement,” says the report. “The key damage caused by cryptomining is based on wasted cost of compute cycles.”
While this may be true for miners, it is worth remembering that the miners found a way in. Given the efficiency of information sharing in the dark web, that route is likely to become known to other criminals. In August 2022, Sophos reported on ‘multiple adversary’ attacks, with miners often leading the charge. “Cryptominers,” Sophos told SecurityWeek at the time, “should be considered as the canary in the coal mine – an initial indicator of almost inevitable further attacks.”
In short, if you find a cryptominer in your cloud, start looking for additional malware, and find and fix the miner’s route in.
The fifth risk is slow vulnerability remediation – that is, an overlong patch timeframe. We have already seen that Log4Shell has a remediation time of more than 136 days, if it is done at all. The same general principle will apply to other patchable vulnerabilities.
Effective patching quickly lowers the quantity of vulnerabilities in your system and improves your security. Statistics show that this is more effectively performed by some automated method. “In almost every instance,” says the report, “automated patching proves to be a more effective remediation path than hoping manual efforts will effectively deploy critical patches and keep your business safer.”
For non-Windows systems, the effect of automated patching is an 8% improvement in the patch rate, and a two-day reduction in the time to remediate.
Related to the remediation risk is the concept of technical debt – the continued use of end-of-support (EOS) or end-of-life (EOL) products. These products are no longer supported by the supplier – there will be no patches to implement, and future vulnerabilities will automatically become zero day threats unless you can otherwise remediate.
“More than 60 million applications discovered during our investigation are end-of-support (EOS) and end-of-life (EOL),” notes the report. Furthermore, “During the next 12 months, more than 35,000 applications will go end-of-support.”
Each of these risks need to be prioritized by defense teams. The speed of cloud use by consumers and abuse by attackers suggests that wherever possible defenders should employ automation and artificial intelligence to protect their cloud assets. “Automation is central to cloud security,” comments Bhatt, “because in the cloud, computing resources are numerous and in constant flux.”
Related: Google Cloud Now Offering $1 Million Cryptomining Protection
Related: Survey Shows Reasons for Cloud Misconfigurations are Many and Complex
Related: Qualys Flags Gaping Security Holes in Exim Mail Server
Related: Most Weaponized Vulnerabilities of 2022 and 5 Key Risks: Report
READ MORE HERE


