Using Zero Trust principles to protect against sophisticated attacks like Solorigate
The Solorigate supply chain attack has captured the focus of the world over the last month. This attack was simultaneously sophisticated and ordinary. The actor demonstrated sophistication in the breadth of tactics used to penetrate, expand across, and persist in affected infrastructure, but many of the tactics, techniques, and procedures (TTPs) were individually ordinary.
Companies operating with a Zero Trust mentality across their entire environment are more resilient, consistent, and responsive to new attacks—Solorigate is no different. As threats increase in sophistication, Zero Trust matters more than ever, but gaps in the application of the principles—such as unprotected devices, weak passwords, and gaps in multi-factor authentication (MFA) coverage can be exploited by actors.
Applying Zero Trust
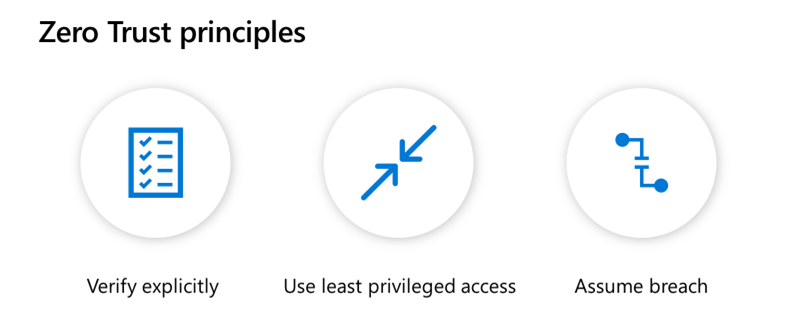
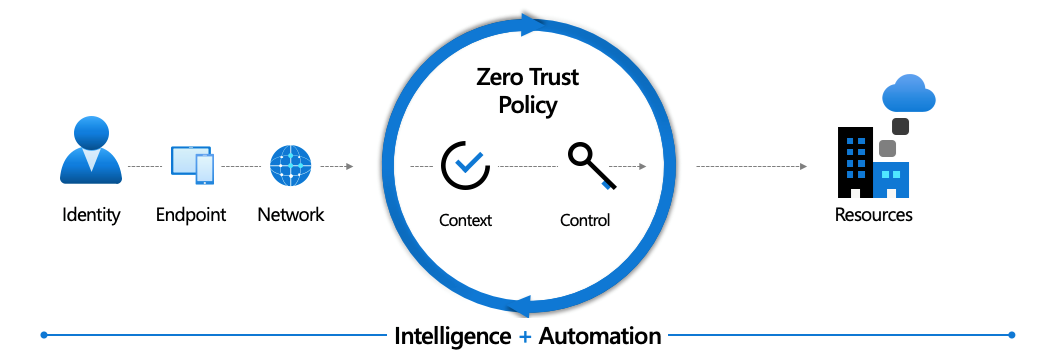
Zero Trust in practical terms is a transition from implicit trust—assuming that everything inside a corporate network is safe—to the model that assumes breach and explicitly verifies the security status of identity, endpoint, network, and other resources based on all available signals and data. It relies on contextual real-time policy enforcement to achieve least privileged access and minimize risks. Automation and Machine Learning are used to enable rapid detection, prevention, and remediation of attacks using behavior analytics and large datasets.
Verify explicitly
To verify explicitly means we should examine all pertinent aspects of access requests instead of assuming trust based on a weak assurance like network location. Examine the identity, endpoint, network, and resource then apply threat intelligence and analytics to assess the context of each access request.
When we look at how attackers compromised identity environments with Solorigate, there were three major vectors: compromised user accounts, compromised vendor accounts, and compromised vendor software. In each of these cases, we can clearly see where the attacker exploited gaps in explicit verification.
- Where user accounts were compromised, known techniques like password spray, phishing, or malware were used to compromise user credentials and gave the attacker critical access to the customer network. On-premises identity systems are more vulnerable to these common attacks because they lack cloud-powered protections like password protection, recent advances in password spray detection, or enhanced AI for account compromise prevention.
- Again, in cases where the actor succeeded, highly privileged vendor accounts lacked protections such as MFA, IP range restrictions, device compliance, or access reviews. In other cases, user accounts designated for use with vendor software were configured without MFA or policy restrictions. Vendor accounts should be configured and managed with the same rigor as used for the accounts which belong to the organization.
- Even in the worst case of SAML token forgery, excessive user permissions and missing device and network policy restrictions allowed the attacks to progress. The first principle of Zero Trust is to verify explicitly—be sure you extend this verification to all access requests, even those from vendors and especially those from on-premises environments.
Cloud identity, like Azure Active Directory (Azure AD), is simpler and safer than federating with on-premises identity. Not only is it easier to maintain (fewer moving parts for attackers to exploit), your Zero Trust policy should be informed by cloud intelligence. Our ability to reason over more than eight trillion signals a day across the Microsoft estate coupled with advanced analytics allows for the detection of anomalies that are very subtle and only detectable in very large data sets. User history, organization history, threat intelligence, and real-time observations are an essential mechanism in a modern defense strategy. Enhance this signal with endpoint health and compliance, device compliance policies, app protection policies, session monitoring, and control, and resource sensitivity to get to a Zero Trust verification posture.
For customers that use federation services today, we continue to develop tools to simplify migration to Azure AD. Start by discovering the apps that you have and analyzing migration work using Azure AD Connect health and activity reports.
Least privileged access
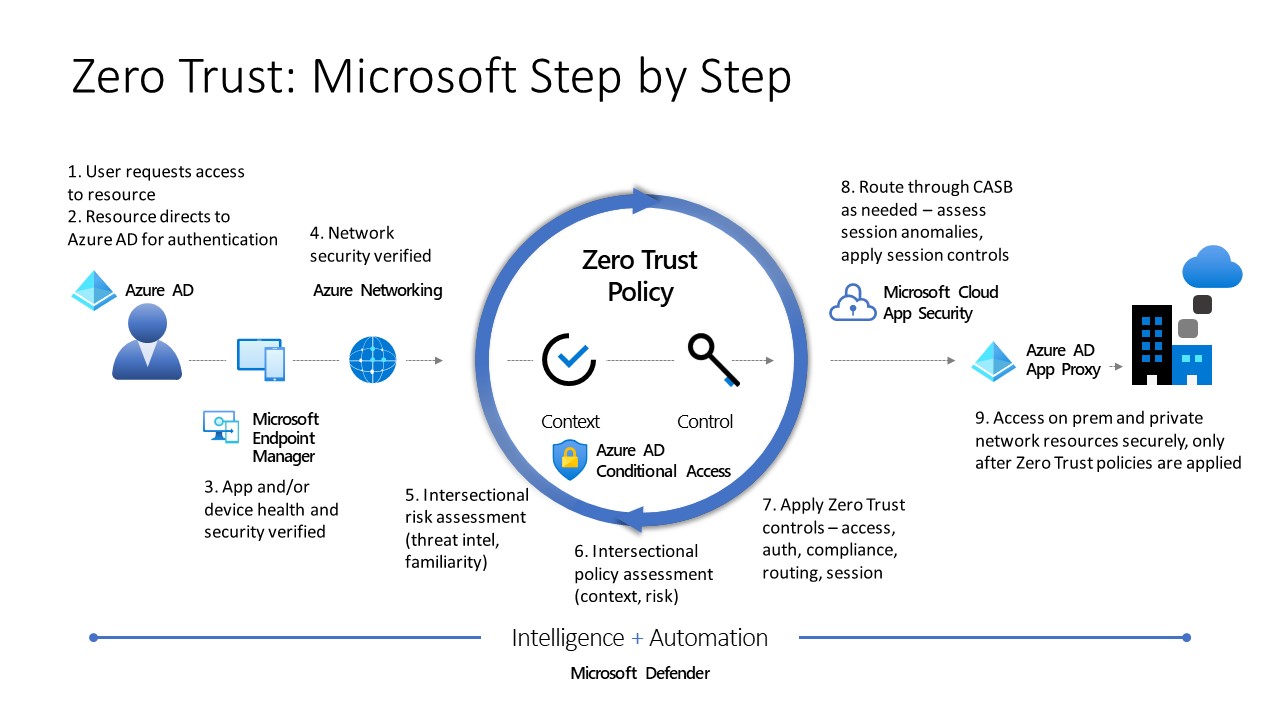
Least privileged access helps ensure that permissions are only granted to meet specific business goals from the appropriate environment and on appropriate devices. This minimizes the attacker’s opportunities for lateral movement by granting access in the appropriate security context and after applying the correct controls—including strong authentication, session limitations, or human approvals and processes. The goal is to compartmentalize attacks by limiting how much any compromised resource (user, device, or network) can access others in the environment.
With Solorigate, the attackers took advantage of broad role assignments, permissions that exceeded role requirements, and in some cases abandoned accounts and applications which should have had no permissions at all. Conversely, customers with good least-privileged access policies such as using Privileged Access Workstations (PAW) devices were able to protect key resources even in the face of initial network access by the attackers.
Assume breach
Our final principle is to Assume Breach, building our processes and systems assuming that a breach has already happened or soon will. This means using redundant security mechanisms, collecting system telemetry, using it to detect anomalies, and wherever possible, connecting that insight to automation to allow you to prevent, respond and remediate in near-real-time.
Sophisticated analysis of anomalies in customer environments was key to detecting this complex attack. Customers that used rich cloud analytics and automation capabilities, such as those provided in Microsoft 365 Defender, were able to rapidly assess attacker behavior and begin their eviction and remediation procedures.
Importantly, organizations such as Microsoft who do not model “security through obscurity” but instead model as though the attacker is already observing them are able to have more confidence that mitigations are already in place because threat models assume attacker intrusions.
Summary and recommendations
It bears repeating that Solorigate is a truly significant and advanced attack. However ultimately, the attacker techniques observed in this incident can be significantly reduced in risk or mitigated by the application of known security best practices. For organizations—including Microsoft—thorough application of a Zero Trust security model provided meaningful protection against even this advanced attacker.
To apply the lessons from the Solorigate attack and the principles of Zero Trust that can help protect and defend, get started with these recommendations:
- More than any other single step, enable MFA to reduce account compromise probability by more than 99.9 percent. This is so important, we made Azure AD MFA free for any Microsoft customer using a subscription of a commercial online service.
- Configure for Zero Trust using our Zero Trust Deployment Guides.
- Look at our Identity workbook for Solorigate.
Stay safe out there.
For more information about Microsoft Zero Trust please visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
READ MORE HERE