ViperSoftX Updates Encryption, Steals Data


Figure 11. Top 10 countries affected by ViperSoftX malware in the enterprise (top) and consumer (bottom) sectors
Source: Trend Micro Smart Protection Network (SPN)
Conclusion and insights
While other cybercriminals use sideloading to load another non-binary component (usually the encrypted payload, which comes together as a package with the normal executable and the sideloaded DLL), the chosen techniques of the actors behind ViperSoftX (which involve using WMI Query Language (WQL), DLL sideloading/DLL load order hijacking, PowerShell reflective loading, browser hijacking, and C&C protection) are sophisticated.
The cybercriminals behind ViperSoftX are also skilled enough to execute a seamless chain for malware execution while staying under the radar of authorities by selecting one of the most effective methods for delivering malware to consumers. Although we have observed some changes throughout their campaigns, the pace of ViperSoftX’s development can be considered slow compared to other types of stealer malware.
The group behind this malware has been doing this for a number of years, and it knows its target systems based on the simultaneous use of techniques to steal cryptocurrencies and passwords. In this respect, we believe there are actually at least two groups responsible for this ViperSoftX campaign based on the malware’s C&C communication. As the first set of players, the main group is responsible for the deployments. On the other hand, considering the monthly change of C&C servers and communication exchange, we believe in the possibility of another group involved based on the different coding or C&C scheme. ViperSoftX uses a domain-generating algorithm (DGA) to hide its C&C server and generate useless traffic. From the DGA technique, we observed that majority of the activities are dominated by the main group, which utilizes a simple DGA. However, there are a number of activities that appear to use a different DGA. We do not discount the possibility that these can either be older samples or different operators entirely.
While ViperSoftX appears to be targeting consumers considering its chosen means for entry, we found it interesting that it also affects the business sector. One possible theory behind why businesses are affected by this campaign has to do with recent layoffs and possible budget cuts. While some users might be looking to freelance and upend their incomes while in between jobs, others might have been prompted to download tools from unofficial platforms to “save costs” and circumvent tools not found in office-issued devices. Nonetheless, we strongly recommend that users download the software and applications they need from official platforms. Cracks and other illegally owned software will only work for certain periods since majority of license verification methods are now done in the cloud. If features such as updates to circumvent the replacement of cracks or patches are disabled, users would then be putting their respective systems at greater risk of attacks or infections.
Here are some additional recommendations to prevent the risks of infection from malware types like ViperSoftX:
- Download software and applications from official platforms and sources.
- Instead of downloading illegal software, choose alternative freeware solutions from reputable sources and platforms.
- Download security solutions that can detect and block malicious components in seemingly legitimate and non-malicious software and applications.
Trend Micro solutions
Trend Micro customers are protected from threats like ViperSoftX with Trend Micro Vision One™, which provides multilayered protection and behavior detection, thereby blocking questionable behavior and tools before a piece of malware can do any damage. Implementing a multifaceted approach can aid organizations in securing potential entry points into their systems such as endpoint, email, web, and network. With the help of security solutions that can identify malevolent elements and questionable activities, enterprises can be safeguarded via automated protection while also ensuring that no significant incidents go unnoticed.
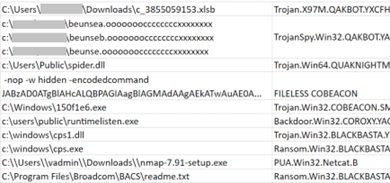
Indicators of Compromise (IOCs)
The list of IOCs can be downloaded here.
Read More HERE